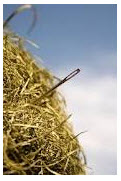
If too much logging occurs, it makes the value next to nothing and more like searching for a needle in a haystack. There’s also the risk of logs being overwritten if they aren’t set to handle all the events. It’s essential to know what is necessary and only audit those changes instead of using a broad approach hoping critical problems will jump out at you. Trying to keep up with all the native security data each day is nearly impossible without the proper resources. But what if you aren’t ready or able to commit to only a few aspects and need a broader overview? This is where you need the help of a tool that can automatically gather all the logs, remove unnecessary noise and produce readable reports in plain language you can understand.
Fact is, organizations that implement audit logging are far less at risk of a security or compliance problem than without even if they may be unsure at the outset what is and isn’t important. With Netwrix Change Reporter Suite, you can audit effectively and easily without the massive volumes of raw data and monitor changes that are important. In addition to Windows Servers, this solution audits changes to Active Directory, Group Policy, Exchange, SQL, SharePoint, VMware, EMC, NetApp, File Servers, Network Devices such as Cisco firewalls and more. It shows who made what change, when and where as well as many before and after settings in easy-to-read reports. It scales to environments large or small, sets up quickly and is cost-effective.
Have you tried Windows security auditing on your own successfully (be honest!)? What were the results? How more/less effective were you at maintaining Windows security before/after implementing a procedure to audit your environment or more specifically, your Windows systems? Please share your experiences, thoughts and comments below:

