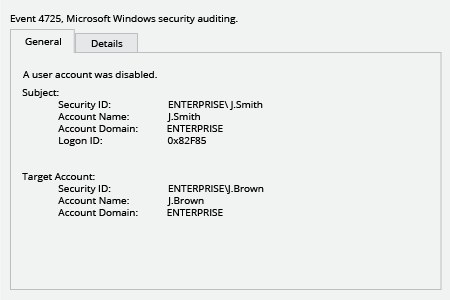
If a user can’t log into IT systems with Windows authentication, one of the reasons behind could be an accidentally performed change to system configuration. An incorrect change to system configuration can accidentally disable a user in Active Directory. Disabled users in Active Directory may be unable to access critical resources such as email, files and SharePoint, disrupting the seamless flow of operations. Therefore, IT pros needs to be able to detect when accounts are disabled and quickly determine who made the changes that resulted in Active Directory disabled account.
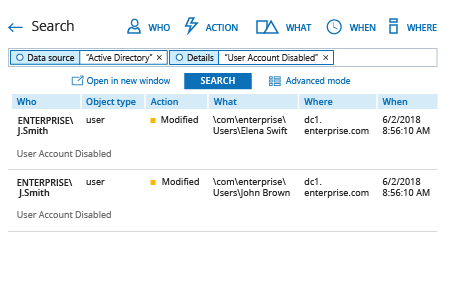
Netwrix Auditor for Active Directory offers a Google-like Interactive Search feature that helps IT pros detect Active Directory disabled accounts. It also includes a predefined report that shows changes to user account status, including details about who made each change that disabled users in Active Directory and when the change was made. Moreover, Netwrix Auditor for Active Directory can send a real-time alert whenever there’s a status change in an Active Directory account, empowering IT pros to detect disabled user accounts much faster.