During my 20+ year career in IT, I have been involved in projects from many different angles. I have been an end user and a consultant; I have managed technology and I have sold it. But throughout it all, there has been one constant challenge: How to assess the return on investment for a technology you either provide or consume.
My journey has led me to IT security, and I often hear statements like, “It’s hard to measure the effectiveness of security investments. It’s like insurance: you know you need it, but you can’t put a value on it.” But this attitude is a no-go if you want to be an effective IT manager. You absolutely need a method for accurately calculating your return on security investment (ROSI), so you can assess whether your cyber security strategy is meeting the goals of your department and your organization, and, if necessary, argue for additional budget. In this blog post, I describe how to calculate ROSI.
Classic return on investment
Return on investment (ROI) is a profitability ratio for a specific investment. It helps you determine whether you should make a purchase or skip it, or how a particular investment has performed to date.
The simplest way to calculate ROI is to quantify some kind of “return” or “benefit” and divide it by the “investment” or “cost”:
Calculating ROI
Why classic ROI doesn’t work for return on security investment
This ROI equation works only for investments that yield positive results, such as cost savings or revenue enhancements. But what is a security investment? This kind of investment neither increases revenues directly nor provides immediate payback; rather, security investments are about risk management that results in loss prevention and risk mitigation. Thus, a ROSI calculation should indicate how much loss the organization could avoid due to the security investment, so we need a different formula.
Choosing the right metrics for ROSI
Before we dive into how to calculate ROSI, it’s important to ensure that the process is practical and delivers reliable and actionable results. It’s essential to make sure that your metrics are:
- Easy to gather on a regular basis. If it costs a lot of time or money to gather the data you need, ROSI calculation will very quickly become a burden and outweigh any perceived benefit.
- Relevant to your business and the risks it faces.
- Relatively accurate. Since you are estimating threats that could strike your company, your calculations won’t be 100% accurate. Accept that and do the best you can.
Calculating ROSI — the quantitative risk analysis formula
The SANS Institute offers a quantitative risk analysis formula for estimating ROSI that has been widely adopted. Unlike simple ROI formulas, it is based on your assessment of the specific risks that a given security investment will address. Therefore, you need to clearly understand your security risk exposure and estimate the value of each asset that the security investment aims to protect. Here’s the formula:

Quantitative risk analysis formula for calculating ROSI
Let’s explore how to calculate each of the components in this formula.
-
Annualized loss expectancy (ALE)
The annualized loss expectancy (ALE) is the total annual monetary loss per year expected to result from a specific exposure factor if the security investment is not made. To calculate ALE, we multiply the single loss expectancy (SLE) by the annualized rate of occurrence (ARO):

Calculating ALE
Here are the two components of the ALE formula:
- Single loss expectancy (SLE) is the amount of money that will be lost in a single security incident. To estimate SLE, you need to inventory your data and other IT assets and add up the direct costs (e.g., technical investigations and legal penalties) and indirect costs (e.g., business downtime and increased customer churn rate) of damage to or loss of those assets.
- Annualized rate of occurrence (ARO) is the estimated frequency or expectancy of a threat striking within a year. This is a straightforward number and you can glean from historical records. For instance, if a certain threat has struck your organization only once in the last 10 years, it has an ARO of 0.1; if a threat occurs about 10 times each year, it has an ARO of 10.
-
Mitigation ratio
The mitigation ratio is the percentage of risks that the security investment would address.
According to Sonnenreich, Albanese and Stout — some of the first researchers to tackle the problem of quantifying the value of security controls — it’s ok if your risk mitigation ratio is approximate. The best approach is to assess the predicted number of mitigated risks based on a scoring algorithm you choose yourself. Even if the data for the ROSI model is inaccurate, using this algorithm in a repeatable and consistent way will enable you to comparing the relative value of different security investments.
Example
Let’s estimate the ALE and mitigation ratio for a fictional scenario and use them to calculate the ROSI for a proposed security investment.
Suppose you know that your file servers have shared folders containing files with sensitive information that are accessible by everyone in your company. You know that this data overexposure increases the risk of data compromise and loss, but you don’t know the exact number or location of the folders. To reduce this risk, your company is considering investing in a solution for discovering sensitive data. To determine whether this investment is justified, you need to do the math.
You predict that if you don’t have the solution, you’ll have an average of 10 security incidents per year (ARO = 10). Each incident could lead to a breach costing around $40,000 in data loss, fines, lost productivity and lost business (SLE = 40,000). Therefore, the ALE is 400,000.
The proposed data discovery solution is expected to mitigate this risk by 94% (mitigation ratio = 94%). The estimated cost of buying and managing the solution is $60,000.
So you can calculate the using the ROSI formula from above as follows:
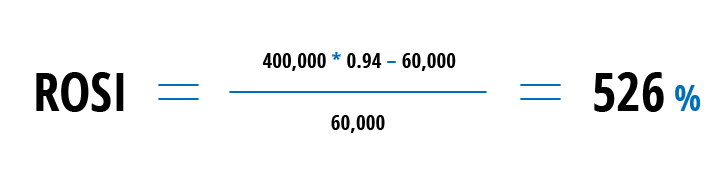
Sample ROSI calculation
Using this calculation, you can argue that this investment will save the company about $316,000 ($400,000 * 0.94 – $60,000), for a 526% payback.
You can also use this formula to evaluate the ROSI of an existing investment. Just be sure to conduct an accurate risk assessment and understand your company’s risk exposure.
Modifying the ROSI formula with additional metrics
You can modify the quantitative risk analysis formula by including additional criteria that are industry-specific or just more important for your organization. Here are some examples:
- Risk profile versus industry peers — Comparing your security budget and execution to your peers in your industry can be quite useful. Industry-specific research will help you identify quantitative best practices, learn what threats your peers encounter and how they address them, and see baselines to orient yourself. I advise starting with research conducted by Gartner.
- Compliance status — If your company is subject to a new compliance standard or wants to improve its compliance with an existing one, you should include your compliance status as a factor when evaluating security investments. You can gather this data by conducting regular internal audits to check whether your processes align with the security frameworks mandated by the standard, checking your grades on recent audits, and determining what areas you need to work on.
- Organizational readiness to address incidents — I wrote about security simulations (“war-gaming”) in another blog post. You divide your security pros into two groups: One team attacks your infrastructure and the other group defends it. By conducting these games every once in a while, you will be able to track performance of your team members during the attack, test the effectiveness of your security program and investments, and compare the results you achieve with the previous games. For example, you can look at how much time the team needed to detect and respond to the attack and which individuals performed better and who needs additional training.
Conclusion
Taking the time to calculate ROSI before you make investments and regularly calculating it for existing investments can deliver more benefits than you might think. Accurately calculated, ROSI will give you the actionable and reliable data you need to figure out whether your efforts actually support your IT security strategy and reduce cyber risks, determine whether your current security spending is justified, adjust your budget by reallocating resources to priority issues, or request additional investments.

.png)