If you’re a knowledge worker, to be productive in a work environment, you’re probably going to need a user account. And you’re probably going to need to actually use this user account to login to your office and mobile devices. If you don’t, you’re probably not going to be working at that company for too much longer.
As IT administrators, we see users log on and off all the time. When Active Directory (AD) auditing is setup properly, each of these logon and logoff events are recorded in the event log of where the event happened from. With enough scripting kung-fu or specialized software we could, fairly easily, pull all of these logon and logoff events since each event has a unique ID. However, there’s no way to know how long that user account was logged on. Using a little patience and event log snooping we can.
To figure out user session time, you’ll first need to enable three advanced audit policies; Audit Logoff, Audit Logon and Audit Other Logon/Logoff Events. The combination of these three policies get you all of the typical logon/logoff events but also gets the workstation lock/unlock events and even RDP connect/disconnects. This ensures we get all of the session start/stop events.
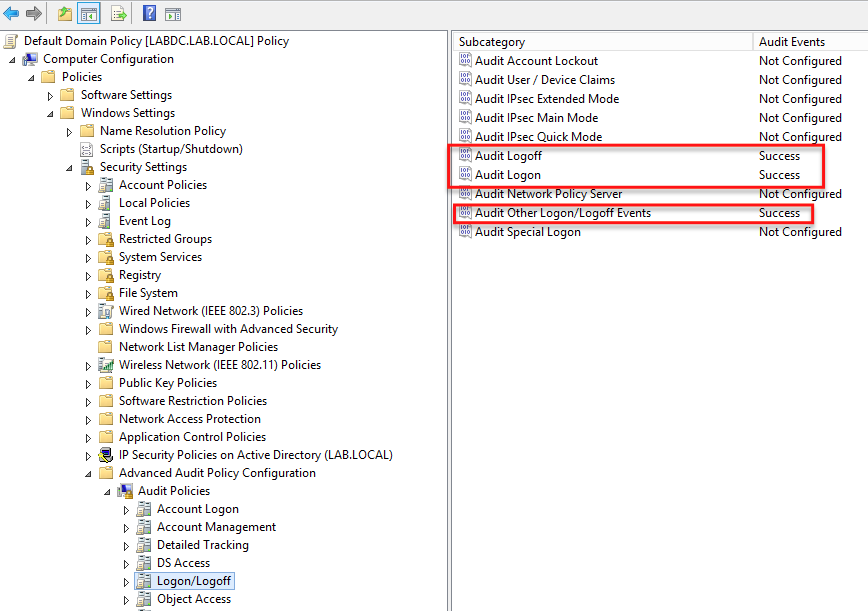
When these policies are enabled in a GPO and applied to a set of computers, a few different event IDs will begin to be generated. They are:
- Logon – 4624 (Security event log)
- Logoff – 4647 (Security event log)
- Startup – 6005 (System event log)
- RDP Session Reconnect – 4778 (Security event log)
- RDP Session Disconnect – 4779 (Security event log)
- Locked – 4800 (Security event log)
- Unlocked – 4801 (Security event log)
You’ll notice the startup event. Why that one? The reason is because what if the computer’s power plug is pulled while a user is logged in? How will we know when that is. It’s not a perfect metric but it’s the only date/time we have to show when that happened.
Once we’ve got all of the IDs put together, we’ll then need to match the session start event with the very next session end event. But what if there are multiple users logging into a computer? To differentiate we can use the Logon ID field. This is a unique field for each logon session. If we can find a session start time and then look up through the event log for the next session stop time with the same Logon ID we’ve found that user’s total session time.
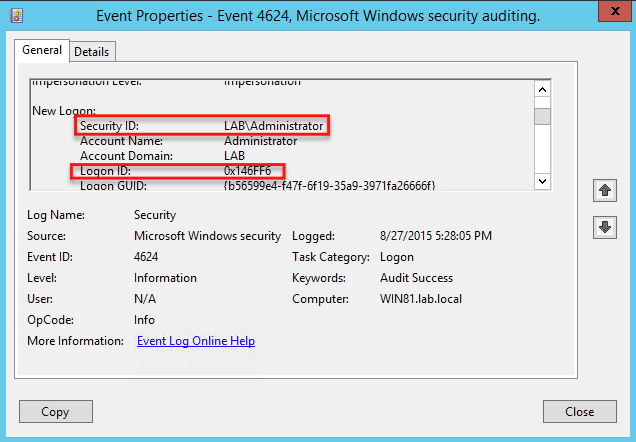
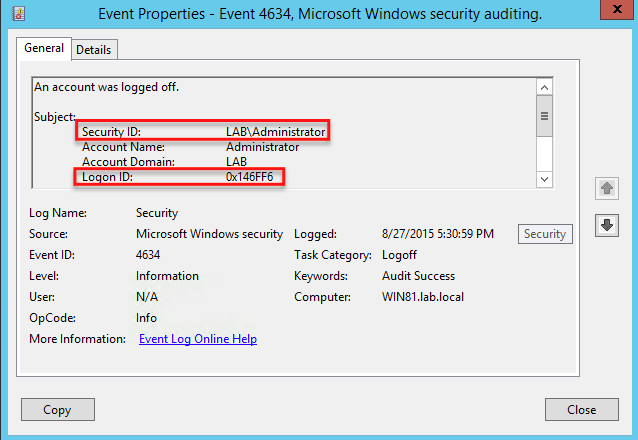
In this instance, you can see that the LABAdministrator account had logged in (ID 4624) on 8/27/2015 at 5:28PM with a Logon ID of 0x146FF6. I then looked up through the event log at the subsequent messages until I found a session end event (ID 4634) that showed up with the same Logon ID at 5:30PM on the same day. Knowing this Logon ID, I was then able to deduce that the LABAdministrator account had been logged on for three minutes or so.
This was just a quick demonstration of actual logon/logoff scenarios. You’ll find that when you review a computer in the “real world” you can’t always depend on logon/logoff events if you’d like to find user session durations. Multiple scenarios may come into play such as when a user locks her computer and comes back to unlock it. Perhaps she may lock her computer and the power gets cut. There will be no unlock event; only a startup event. These are the gotchas you need to watch out for to be able to accurately calculate user session history.



