Imagine that you get a phone call from the security specialist who handles your firewalls and proxy servers. He tells you that he has added an additional proxy server for users going to the internet. You add a new GPO that affects all users so they can use the new proxy server via Internet Explorer. Usually, it takes between 90 and 120 minutes for a new GPO to be applied, but you need the new settings to be applied right now, and you cannot tell your users to log off and log back in to apply them. In cases like these, you might want to bypass the normal wait time before background policy processing kicks in. You can do so using the command prompt, the Group Policy Management Console (GPMC) or PowerShell.
What is GPUupdate
Group Policy is a valuable feature of Active Directory that enables administrators to apply a wide range of settings to users and computers. It is critical for security and productivity that changes to Group Policy objects (GPOs) and new GPOs be applied in a timely manner.
Accordingly, Group Policy is automatically refreshed whenever a domain member computer is restarted or a user logs on to it. It is also automatically updated at a defined background refresh interval (by default, every 90 minutes with a randomized offset of up to 30 minutes).
Sometimes, however, administrators need apply GPO settings to client systems immediately, such as when they create a new policy or make an important change to an existing policy. Furthermore, sometimes they want to not only apply changes but also reapply GPOs that have not been changed usually in order to revert unwanted changes made on local machines.
This document walks you through the ways in which you can force a Group Policy refresh.
GPUpdate vs GPUpdate /force command
The gpupdate /force command is one of the most frequently used commands for updating group policy. The /force switch enables administrators to re-apply all policy settings. However, it’s important to consider that using the /force switch would result in a significant load on Domain Controllers (DCs), especially when there is a large number of Group Policy Objects (GPOs) in the environment.
If you have a substantial tenancy or a large number of GPOs, it is preferable to run gpupdate without the /force switch to implement new policy settings. This approach will only receive changes or new group policies, thereby reducing the workload on both the client and domain controllers.
How to force group policy update
To force a Group Policy update, you can use any of the following options:
- The gpupdate /force command
- The Group Policy Management Console (GPMC)
- PowerShell
Prerequisite: Configure Firewalls before Applying GPOs
Before forcing reapplication of GPOs using any of these options, make sure the firewalls permit inbound network traffic on the applicable ports (by default, TCP port 135), as detailed in the Microsoft documentation.
Force a Group Policy Update using the Command Prompt
gpupdate is a Microsoft Command shell command for Group Policy update on Active Directory computers. It is included in all Window OS versions.
The /force Parameter
Running the gpupdate command with no parameters applies only changed policy settings and new GPOs. But sometimes you need to also re-apply all GPOs that have not changed – such as to revert unwanted modifications made by local administrators (or adversaries who have compromised their accounts).
In that case, you need to use the /force parameter, as follows:
gpupdate /force
There are two key considerations to keep in mind when using this parameter to update Group Policy settings:
- You must physically trot out to each user machine and run the gpupdate /force command manually. (To update computers remotely, use PowerShell, as described below.)
- Using the /force switch can result in significant load on DCs and clients, especially when there are large number of GPOs in an environment. In those cases, it is preferable to run gpupdate without the /force parameter.
Additional Parameters
Running gpupdate while a user is logged on to a machine immediately gives Windows the new GPO settings (assuming, of course, that the domain controller has the replicated GPO information).
If the user is not logged on, in Windows XP and later, by default, GPO settings are processed only at the next logon time. But if you use the right switches, gpupdate can figure out if newly changed items require a logoff or reboot to be active:
- /Logoff – Using this switch will figure out if a policy change requires the user to log off. If not, the new settings are applied immediately; if so, the user will automatically be logged off and the Group Policy settings will be applied when they log back in.
- /boot – Similarly, if Fast Boot is enabled, a restart is required to apply GPOs that have Software Distribution settings. Running gpupdate with the /boot switch will figure out if a policy has something that requires a reboot and automatically reboot the computer. If the updated GPO does not require a reboot, the GPO settings are applied, and the user remains logged on.
Both the /Logoff and /boot switches are optional.
Other useful switches options are available in conjunction with /force
- /Logoff– Log the user off after the Group Policy settings have been updated.
- /Sync – Change the foreground (startup/logon) processing to synchronous.
- /Target – Indicates whether to update policy settings for only Users or Only Computers. Both User and Computer policy settings are updated by default.
- /Boot – Restart the machine after the Group Policy settings are applied.
Force a group policy update using the Group Policy Management Console (GPMC)
The second way to force a Windows Group Policy update is to use the Group Policy Management Console. While the gpupdate command updates all policies for all OUs, GPMC gives you the option to limit the update to a specific OU. Take these steps:
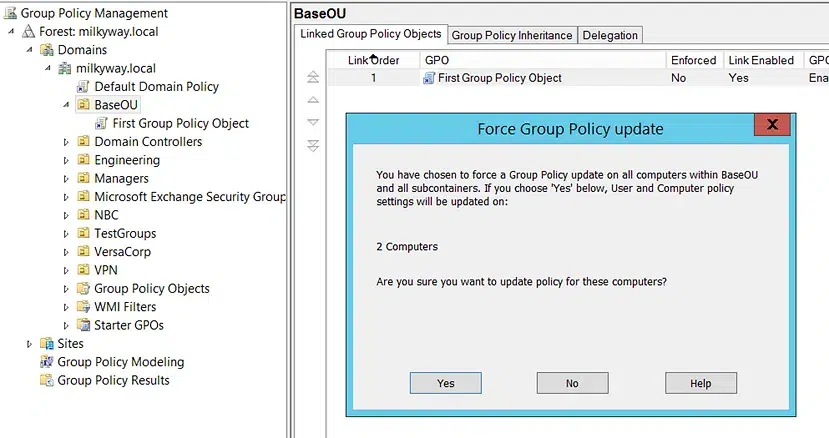
- Open the GPMC (Group Policy Management Console)
- Link the GPO to an OU.
- Right-click the desired OU and choose Group Policy Update” option.
- Confirm the action In the Force Group Policy Update dialog that appears, by clicking Yes.
Force group policy update remotely on computers using Powershell
To update Group Policy remotely, you need to use Powershell. Since Windows Server 2012, you can use the cmdlet Invoke-GPUpdate. to force a Group Policy remote update on Windows client computers. You will need to have both PowerShell and the Group Policy Management Console installed. The cmdlet produces no output.
Examples of using Involve-GPUpdate for Remote Group Policy Update
Another advantage of using the Invoke-GPUpdate cmdlet is that the “RandomDelayInMinutes” option allows you to adjust the delay. If you want to an immediate Group Policy update, set it to 0, as shown here:
Invoke-GPUpdate –Computer LHE-LT-ADAM -RandomDelayInMinutes 0In this instance, a computer identified as “LHE-LT-ADAM” was immediately restarted the after starting a Group Policy update. The cmdlet produces no output. The only downside to using this parameter is that the users will get a cmd screen pop-up.
If you want to force an update on all computers, run the code below. It will get all computers from the domain, put them into a variable, and run the commands for each object.
$compgpoupd = Get-ADComputer -Filter *
$compgpoupd | ForEach-Object -Process {Invoke-GPUpdate -Computer $_.name -RandomDelayInMinutes 0 -Force}
The only downside to using the RandomDelayInMinutes parameter is that the users will get a cmd screen pop-up.
This code will get all computers from the domain, put them into a variable and run the commands for each object.
Configure firewalls before applying GPOs
Make sure the firewalls permit inbound network traffic on particular ports before opening your GPMC. Starting from Windows Server 2012, there is a starter GPO in Group Policy Editor called “ The Group Policy Remote Update Firewall Ports”, which verifies whether TCP port 135 is set up for remote scheduled task management.
To enable Windows Firewall with Advanced Security with a GPO:
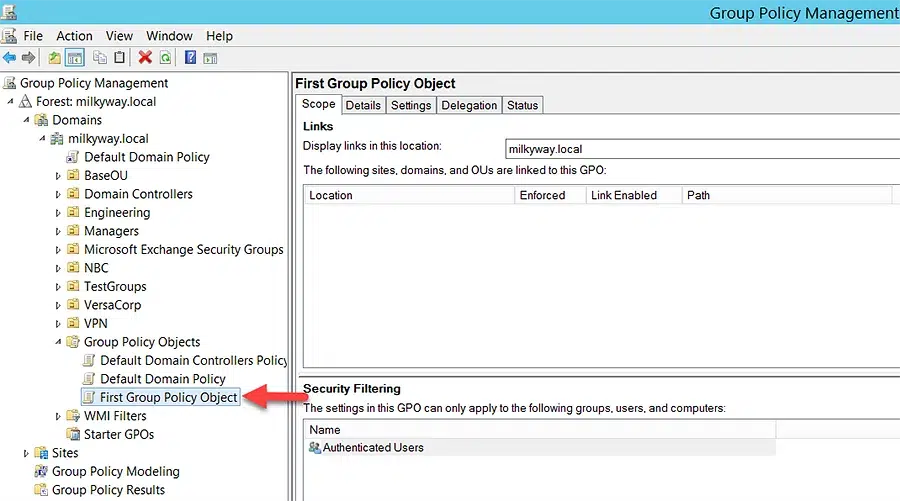
- Launch the interface for Group Policy Management.
- In the navigation pane, expand the following: Forest (YourForestName) => Domains (YourDomainName) => Group Policy Objects: (YourDomainName) => right-click the GPO you wish to edit, and select Edit.
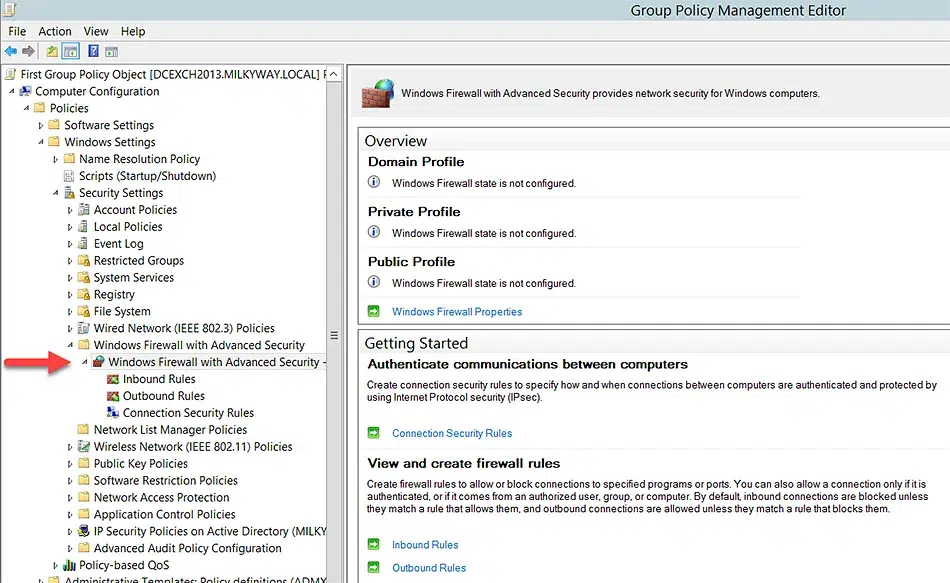
- From the navigation bar of the Group Policy Management Editor, Select Computer Configuration => Policies => Windows Settings => Security Settings => Windows Firewall with Advanced Security => Advanced Security for Windows Firewall.
GPO background refresh
All Group Policy clients process GPOs when the background refresh interval comes to pass – but they process only those GPOs that are new or have changed since the last time the client requested them.
However, for security settings, the Group Policy engine works differently. It asks for a special background refresh just for security policy settings. This is called the background security refresh and is valid for every version of Windows Server. Every 16 hours, each Group Policy client asks Active Directory about all the GPOs that contain security settings (not just the ones that have changed) and reapplies those security settings. This ensures that if a security setting has changed on the client (behind the Group Policy engine’s back), it’s automatically reverted to the proper setting within 16 hours.
Background refresh process for local GPOs
As noted earlier, one key reason you might need to force a Group Policy refresh is that local administrators (or adversaries or have compromised their accounts!) can make changes to settings on their machines that nullify a policy you’ve set with a GPO. Those changes can hurt productivity or even security. For example, a local admin might override your GPO setting that prohibits USB drives, enabling both data theft and introduction of malware.
Accordingly, you should grant local administrator rights only when they are truly needed. Regular users should never be given local admin rights.
Mandatory reapplication of non-security group policy settings
As noted above, the regular background update applies only to new and changed GPOs. However, you can modify the regular background refresh to reapply certain settings, even if the GPOs haven’t changed. This is a good way to fix exploits that aren’t security related.
Specifically, you can choose to mandate the reapplication of the following areas of Group Policy during each initial policy processing and background refresh:
- Registry (Administrative Templates)
- Microsoft Edge Maintenance
- IP Security
- EFS Recovery Policy
- Wireless Policy
- Disk Quota
- Scripts
- Security
- Folder Redirection
- Software Installation
- Wired Policy
How Netwrix Can Help
Group Policy is an extremely powerful way to manage settings for your Windows infrastructure. But it is also complex. Indeed, after years of mergers and acquisitions, employee turnover, technology changes, and so on, Group Policy becomes nearly impossible to manage effectively using manual method and native tools.
Netwrix Endpoint Policy Manager simplifies Group Policy management and enables you to clean up and consolidate your GPOs. As a result, your organization will enjoy faster login, higher security, better uptime, and fewer misconfigurations.
Conclusion
Keeping Group Policy settings up to date across your IT estate is critical for productivity, security, compliance and more. While GPO changes are automatically applied at the next refresh interval; you can also force a refresh to apply them immediately. As an extra safety measure, you can ensure that certain Group Policy settings are always reapplied, even if they have not changed, in order to revert any unwanted changes made by local administrators.
FAQ
How to update group policy?
To update Group Policy manually, administrators can use the gpupdate /force command, the Group Policy Management Console (GMPC) or PowerShell. /force switch enables the administrators to re-apply all policy settings
What does gpupdate /force do?
Group Policy is updated automatically according to a background refresh schedule. However, sometimes an update or new policy needs to take effect sooner, or the organization needs to revert improper policy changes made by local administrators. In those cases, an administrator can use the gpupdate command with the /force parameter to apply a Group Policy update immediately.
How long does gpupdate /force take to update Group Policy?
The time required to force an update Group Policy depends on the number of policies being applied. Updating a small number of policies can take just a couple of minutes, but typically, the process involves a 90-minute application time plus a 30-minute delay for workload distribution.