NIST SP 800-171 details requirements that all Department of Defense (DoD) contractors have been required to follow for years. The guidelines were updated in 2020, and Revision 3 was published in May 2023.
Netwrix is ready to help organizations achieve, maintain and prove NIST 800-171 compliance. Below, we summarize its key requirements and share recommendations for getting started with the regulation.
What is NIST 800-171?
NIST Special Publication 800-171 covers the protection of controlled unclassified information (CUI) in nonfederal information systems and organizations. It aims to help organizations that provide services to federal or state agencies ensure that systems that process or store CUI are secure and under strict control.
Executive Order 13556 established a government-wide CUI program in order to “standardize the way the executive branch handles unclassified information that needs protection.” Controlled unclassified Information is any information created by the government that is unclassified but still needs protection. This includes emails, electronic files, blueprints, drawings, proprietary company or contractor information (such as sales orders and contracts), and physical records. All the categories of sensitive information protected by NIST 800-171 are outlined in the CUI registry.
Who must comply with NIST SP 800-171 requirements?
NIST SP 800-171 compliance is required for non-federal organizations that process, store or transmit CUI. Examples may include:
- Defense contractors
- Organizations whose contracts with federal agencies entail the creation, handling or storage of CUI
- Healthcare institutions collaborating with the U.S. government, particularly those serving veterans through the VA
- Universities and research establishments funded by federal agencies that use CUI
- Aerospace and aviation companies that contract with NASA or other government bodies
- Manufacturers of products for federal government use, such as military equipment
- IT service providers handling government IT systems or offering cloud services to federal agencies
- Financial institutions managing financial data for government agencies or delivering financial services to the government
- Law firms working on government cases or sensitive legal matters
- Organizations that are part of a government contractor’s supply chain and have access to CUI
How do organizations prove compliance?
While the original NIST SP 800-171 allowed organizations to self-attest to their level of compliance, as of Rev 2, they must undergo evaluations by certified assessors to determine their level of compliance, based on the Cybersecurity Maturity Model Certification (CMMC).
CMMC is an assessment framework and certification program that details a set of cybersecurity maturity levels. In the original CMMC, the levels ranging from Level 1 (Basic Cyber Hygiene) to Level 5 (Advanced/Progressive); version 2 will streamline the model to three levels of cybersecurity and align the requirements at each level with NIST cybersecurity standards. Any business handling CUI must be certified to adhere to the CMMC level required for their contracts.
NIST SP 800-171 Controls
NIST SP 800-171 consists of 14 control families that provide guidelines for protecting CUI. Here are those control families and short checklists to help you ensure that you’re aligning as effectively as possible with the most important NIST security requirements
Access Control
This family is the largest in NIST SP 800-171, with 22 controls. You need to monitor all access events in the IT environment and limit access to systems and data.
NIST SP 800-171 recommends focusing on the following actions:
- Implement the least-privilege principle.
- Control the flow of CUI within the organization and encrypt it on mobile devices.
- Monitor and control remote access.
- Control and restrict the use of mobile devices.
- Separate duties of individuals to help prevent aberrant activities.
- Authorize and protect wireless access using encryption and authentication.
Awareness and Training
This set of controls requires you to ensure that managers, system administrators and other users are aware of the security risks associated with their activities. They have to be familiar with the organization’s security policies and basic cybersecurity practices so they can recognize and respond to insider and outsider threats.
The best way to ensure proper awareness is to give employees security training on a regular basis.
Audit and Accountability
This family consists of 9 controls and requires you to retain audit records to use in security investigations and to keep users accountable for their actions. Organizations need to collect and analyze audit logs to detect unauthorized activities and respond to them promptly.
The following steps will help you implement these controls:
- Review and update audited events.
- Report on failures in audit process.
- Generate reports to support on-demand analysis and provide evidence of compliance.
- Protect audit systems from unauthorized access.
Configuration Management
This family also consists of 9 controls. You have to establish and maintain baseline configurations, which involves controlling and monitoring user-installed software and all changes made to organizational systems.
You will need to focus on the following activities:
- Document all events where access was restricted due to changes to IT systems.
- Employ the principle of least functionality by configuring systems to provide only essential capabilities.
- Restrict, disable or prevent the use of programs, functions, protocols and services that are not essential.
- Blacklist unauthorized software.
Identification and Authentication
This family includes 11 controls designed to prevent unauthorized access to critical systems and mitigate the risk of data loss. You need to be able to verify the identities of users, processes and devices in your network.
Be sure to follow these best practices:
- Use multifactor authentication (MFA) for network and local access.
- Disable user accounts that have been inactive for a long time.
- Create a strong password policy, which involves enforcing a minimum level of password complexity and storing only encrypted passwords.
Incident Response
Organizations must have an incident response strategy that enables prompt response to any incident that could result in a data breach or system downtime.
The best recommendations here are to:
- Implement capabilities to detect, analyze, respond to and report on security incidents.
- Test your incident response plan regularly.
Maintenance
Improper system maintenance can result in disclosure of CUI, so it poses a threat to the confidentiality of that information. Therefore, you are required to perform maintenance regularly.
In particular, be sure to:
- Keep a close watch on individuals and teams that perform maintenance activities.
- Ensure that equipment removed for off-site maintenance does not contain sensitive data.
- Ensure that media containing diagnostic and test programs are free of malicious code.
Media Protection
This control family requires you to ensure the security of system media that contain CUI, which includes both paper and digital media.
You will need to adopt several measures:
- Control and limit access to media.
- Implement cryptographic mechanisms to protect CUI stored on digital media.
- Before disposal, make sure that system media does not contain any CUI.
- Forbid the use of portable storage devices when they have no identifiable owner.
Personnel Security
This rather small family of controls requires you to monitor user activities and ensure that all systems that contain CUI are protected during and after personnel actions, such as employee terminations and data transfers.
Physical Protection
Physical protection includes the protection of hardware, software, networks and data from damage or loss due to physical events.
NIST SP 800-171 requires organizations to:
- Limit physical access to systems and equipment to authorized users.
- Maintain audit logs of physical access.
- Control physical access devices.
Risk Assessment
Organizations that are subject to NIST SP 800-171 have to evaluate potential risks to their IT environments on a regular basis. They also need to scan for vulnerabilities in critical systems and applications and remediate them in accordance with the results of the risk assessment.
Security Assessment
Your organization must monitor and assess its security controls to determine if they are effective enough to help keep your data secure. You need to:
- Have a plan that describes system boundaries, relationships between systems and procedures for implementing security requirements.
- Update that plan periodically.
- Implement an action plan to reduce or eliminate vulnerabilities in critical systems.
System and Communications Protection
This rather large family consists of 16 controls for monitoring, controlling and protecting information that is transmitted or received by IT systems.
In particular, you need to:
- Prevent unauthorized transfer of information.
- Build sub-networks for publicly accessible system components that are separated from internal networks.
- Implement cryptographic mechanisms to prevent unauthorized disclosure of CUI.
- Deny network communications traffic by default.
- Control and monitor the use of mobile code and VoIP technologies.
System and Information Integrity
This group of controls requires you need to quickly identify and correct system flaws, as well as protect critical assets from malicious code.
This includes the following tasks:
- Monitor and immediately respond to security alerts that could indicate unauthorized use of IT systems or another cyber threat.
- Perform periodic scans of IT systems, and scan files from external sources as they are downloaded, opened or executed.
- Update antivirus, anti-malware and related tools as soon as new versions are available.
Best Practices for Compliance with NIST SP 800-171
The following best practices will help you get NIST SP 800-171 compliant:
- Understand the requirements: Take the time to thoroughly study NIST Special Publication 800-171, including it requirements, controls and recommended security practices.
- Classify your data: To comply with NIST SP 800-171, you need to know what CUI your organization handles so you can apply the appropriate security controls to protect it.
- Implement strict access controls: Control access to CUI using strategies like strong authentication, effective password policies, role-based access and regular access reviews.
- Provide regular security training: Educate your employees about cybersecurity best practices and the importance of NIST compliance. Human error is a common cause of security breaches, so keeping your workforce informed and vigilant is crucial.
- Audit activity: Implement continuous monitoring to promptly detect and respond to security threats.
- Have an incident response plan: Develop a comprehensive plan detailing the steps to take in the event of a security breach. Being prepared to respond effectively can significantly minimize the impact of a security incident.
- Manage third-party risks: If you engage with third-party vendors or service providers, ensure they also adhere to NIST compliance standards. Evaluate their security practices and establish clear guidelines for data protection in your contracts.
- Keep records: Maintain detailed records of your compliance efforts, assessments and security incidents. Documentation not only helps demonstrate compliance but also aids in post-incident analysis and improvement.
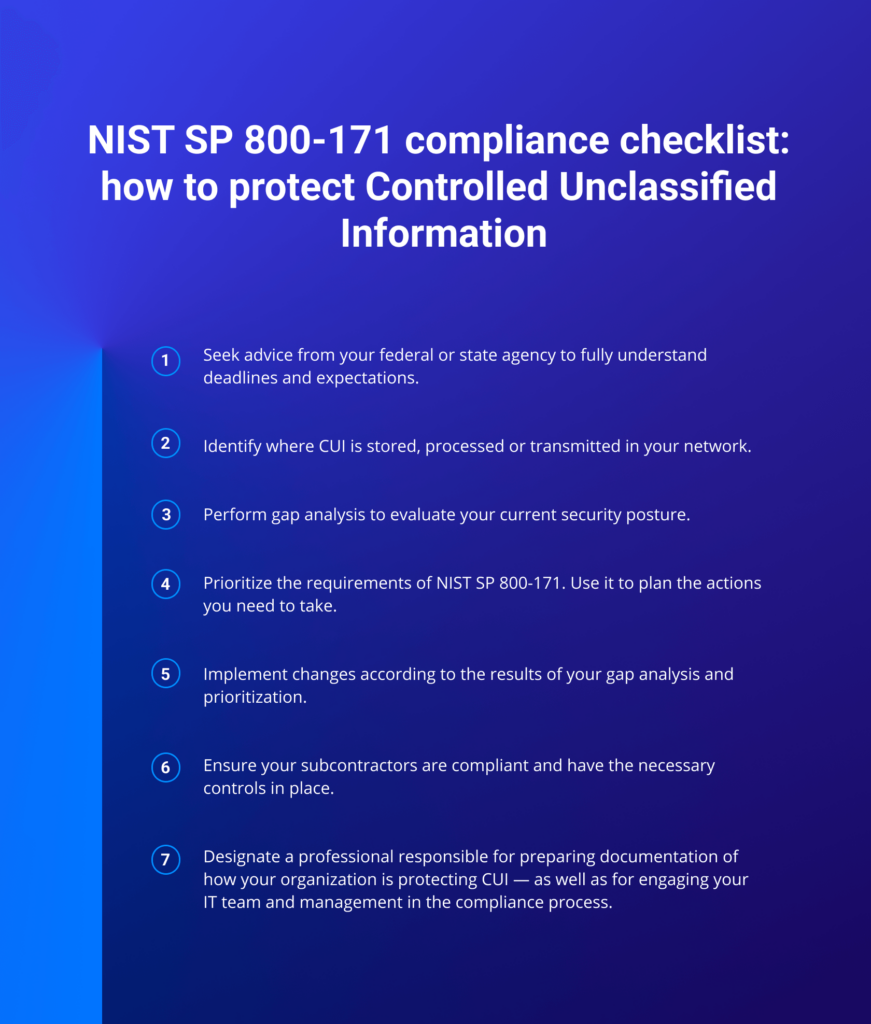
NIST SP 800-171 Compliance Checklist
The following checklist will help you ensure compliance with NIST 800-171:
- Seek advice from your federal or state agency. Even if you are not a DoD contractor, if you provide services to other federal government agencies, there is a good chance that those agencies will ask you to prove your compliance with NIST SP 800-171. You need to make sure that you fully understand what your federal or state agency expects from you and their deadlines.
- Define CUI as it applies to your organization. Identify where CUI is stored, processed or transmitted in your network.
- Perform gap analysis. Evaluate your security posture to determine where you are currently compliant and where you need additional work.
- Prioritize and plan the actions you need to take.
- Implement changes according to the results of your gap analysis and prioritization.
- Ensure your subcontractors are compliant with NIST SP 800-171.
- Designate a person who will be responsible for preparing documentation of how your organization is protecting CUI, as well as for engaging your IT team and management in the compliance process. There are consultants that provide advisory and assessment services to help you with NIST SP 800-171 compliance.
Appendix: Related Guidelines
As we have seen, NIST 900-171 covers how non-federal contractors must protect CUI. Here are two related publications to know about.
NIST SP 800-53
NIST 800-53 covers how federal agencies should build and manage information security systems. It is a supplement to the Federal Information Security Management Act (FISMA), which applies to all federal agencies. It is only around 125 pages and mainly covers the protection of CUI information passing to the internal systems of non-federal organizations. For example, if you’re a contractor for a government agency, you will be guided by NIST 800-171. However, if you’re a federal worker, your department must align with NIST 800-53.
NIST 800-53 includes four additional security controls that are not in NIST-800-171:
- Contingency Planning — Covers actions to prepare for a cybersecurity attack, such as planning and testing backup and recovery processes.
- Planning (Organization-Specific) — Covers security planning, including the policy’s purpose, scope, roles and responsibilities
- Security Assessment and Authorization — Covers conducting security assessments and authorizing access to sensitive data
- Systems and Services Acquisition — Concerns acquiring, developing and managing systems and services throughout their lifecycle.
ISO 27001
ISO 27001 is a standard for information security management systems that is designed for organizations worldwide. It is more flexible than NIST SP 800-171, detailing 114 controls rather specific security requirements. ISO 27001 offers a formal certification option.
Although these frameworks have different areas of focus, they both emphasize the importance of:
- Conducting risk assessments
- Establishing comprehensive information security policies and procedures
- Restricting access to information and information systems based on roles and responsibilities
- Training personnel in how to protect information security
- Developing incident response procedures
- Maintaining documentation and records related to information security
- Assessing the security practices of supply chain partners and establishing security requirements in contracts
Want to know more about NIST Special Publication 800-171? Visit the official page in NIST’s Computer Security Resource Center (CSRC): https://csrc.nist.gov/publications/detail/sp/800-171/rev-1/final