Every business leadership team wants to see a return on its investments. From hiring valuable employees who deliver on projects to securing resources that allow those employees to do their jobs, every cost needs to have a purpose — and investing in security software is no different.
Why does any IT department need ROI evaluation?
IT departments have traditionally been viewed as cost centers or expenses for the sake of risk management. However, the increasing activity of cybercriminals provides an opportunity re-evaluate that assessment and help executives understand how security expenses can actually be viewed as investments with powerful returns.
After all, ROI is about revenue, savings, or productivity. Investing in your technology and security software for the sake of protection against breaches may clearly be a case of risk management, but when your security software affects revenue, savings, or productivity, it’s value is balanced between risk management and an investment that brings a return.
Getting a return on an investment in security is an increasingly popular topic among organizations that see but cannot articulate the ROI of IT. As IT departments shift into sources of cost but also returns, it becomes increasingly useful for IT managers to record and report on data that backs up increases in revenue, savings in expenses, or increased productivity for the business in the form of the following kind of data:
- Network and server upgrades that increase productivity and access to mission-critical applications
- Network installations that increase productivity as related to remote and mobile employees
- Reduced network downtime as compared to previous years
- Preventative security investments and initiatives compared to the cost risk associated with data breach
- Employee training that increases efficiency regarding safety and security protocols
Identifying and sourcing these data points can be difficult because IT managers need to connect potential costs associated with liability to a simple ROI, and the costs associated with security breaches can vary so greatly. IT departments that find it challenging to make this connection can work with a third party to procure a security audit that makes these risk clearer and, therefore, easier to articulate to key stakeholders.
How to calculate ROI for your security software?
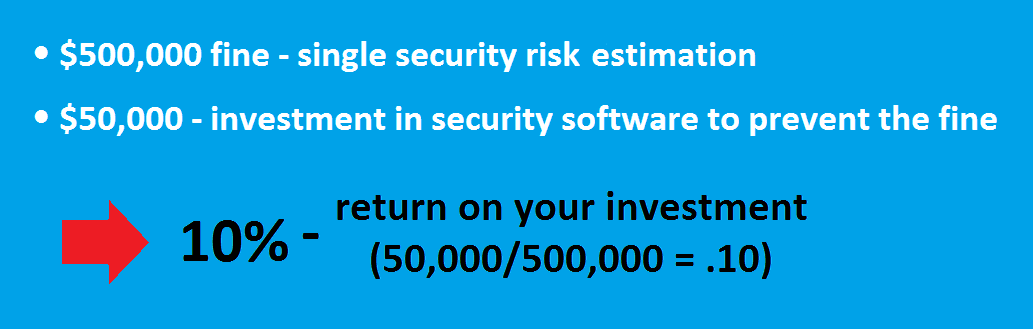
Here is an example formula we recommend IT departments use in order to establish a baseline ROI for investments in security software:
- Identify security risks and translate them into business risks with quantifiable data such as outage time, fines and fees, and opportunity cost of lost performance
- Identify the associated cost with mitigating those quantifiable security risks such as investments in personnel and security software
- Calculate an ROI based on the relationship between the cost of the security risk (X) and the cost of mitigation (Y) as Y/X
Let’s take an example:
A deeper analysis into the year-after-year possibility of the security risk and the tax benefits associated with the investment may make that ROI even greater using scales similar to those used to calculate insurance costs.
If you’re trying to assign a quick and clean ROI to security software investments, you need to reconsider your approach. Security software serves too many functions to be categorized in only one way; instead, it is a balance between risk management and ROI that each company must calculate with its own data points for its own purposes.



