What Is Data Classification?
Simply put, data classification is the process of categorizing files, databases and other content into logical groupings according to their content. For example, a data classification process might distinguish between public information and various types of sensitive data, as well as identify information that is subject to regulatory mandates like the GDPR, HIPAA or the California Privacy Rights Act (CPRA).
Data classification is therefore vital to both data security and compliance, especially for organizations that store large volumes of sensitive or protected data. Classifying data also improves user productivity and decision-making, and reduces storage and maintenance costs by empowering you to eliminate unneeded data.
In this article, you will learn more about the purpose and benefits of data classification, the steps in the data protection process, best practices, and tips for getting a program approved. Finally, you’ll get a guide to help you determine the best solution for your organization.
Types of Data Classification
At a high level, most organizations use a basic strategy to classify data: They manually organize data into folders and subfolders based on their contents. For instance, mortgage applications might be sorted into the Finance category, while offer letters may fall under Human Resources. Windows and other operating systems even come with some basic categories, like Music, Videos and Documents.
However, this is not what the term “data classification” refers to in the world of data security. Rather, data classification means to categorize data based on its sensitivity, which is indicated by who should be permitted to access and use the data. For example, categories might include Top Secret and Confidential for data that needs to be restricted to specific audiences, and Public for information that can be shared freely.
Here are some examples of sensitivity-based classification schemas:
Example Commercial Classification
The data classification schemes used by private organizations typically have three or four levels, such as this one:
- Public: Data that can be freely disclosed, such as your company’s contact information and browser cookie policy
- Proprietary: Information that is private but has low sensitivity, such as organizational processes
- Confidential: Data that has higher security requirements, like competitor research. vendor contracts and employee reviews
- Sensitive: Highly sensitive data whose disclosure could disrupt operations or put the organization at financial or legal risk, such as intellectual property, bespoke applications or healthcare records.
Example Government Classification
Government agencies often use the following levels when classifying data:
- Top Secret: Cryptologic and communications intelligence
- Secret: Select military plans
- Confidential: Data indicating the strength of ground forces
- Sensitive unclassified (or “CUI”): Data tagged “For Official Use Only”
- Unclassified: Data that may be publicly released with authorization
Data Classification Process
The data classification process comprises the following steps:
Step 1. Categorize the Data
The first step in the data classification process is to determine what type of information a piece of data is. To automate this process, organizations can specify specific words and phrases to look for, as well as define regular expressions to find data that follows a certain pattern, such as credit card numbers or medical procedure codes.
Step 2. Label the Data
Once a piece of data has been categorized, It’s important to record that decision for future use. There are several ways to do this:
- Tagging — Another options is to place a digital tag on each file, such as the tags offered by Microsoft Office. Users can search for content based on these tags, and they can be also used by security tools such as data loss prevention (DLP) solutions.
- Extended file metadata — Many modern collaboration platforms can add metadata to content without changing the file itself. For instance, SharePoint, Box, Dropbox and Google Drive can add metadata to a file to improve searchability and classification.
Step 3. Repeat
It’s important to remember that data classification is not a once-and-done process. Not only is new data constantly being created and collected, but existing data can change classification due to new contractual obligations and modifications to internal policies or legal mandates.
Benefits of Data Classification
Understanding what types of data you’re storing and where brings many benefits, including improved data security and regulatory compliance.
Data Security
Classifying your data improves data security by enabling you to:
- Prioritize your security efforts and apply appropriate security controls based on data sensitivity.
- More easily understand who can access, modify or delete certain types of data.
- Improve risk management processes by providing insights like the potential business impact of a breach or ransomware attack.
Regulatory Compliance
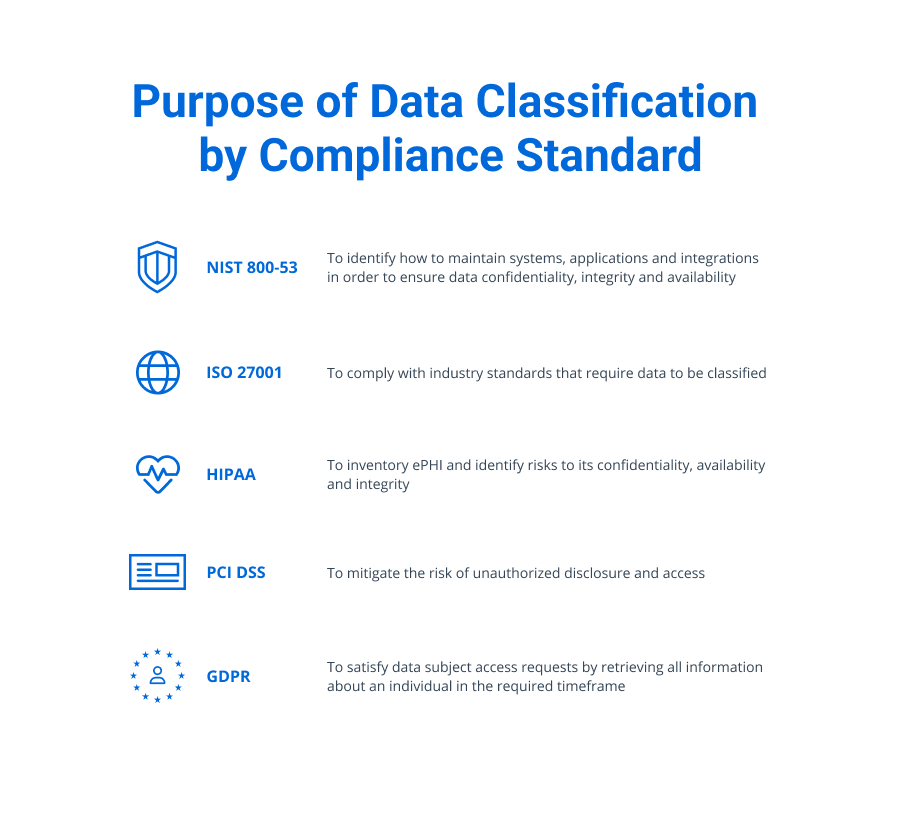
Data classification can identify data that is subject to various compliance regulations so you can protect it as required and pass audits. Here’s how data classification can help you meet common compliance standards:
- GDPR: Data classification helps you uphold the rights of data subjects, including fulfilling data subject access requests by quickly retrieving documents that contain a given individual’s data.
- HIPAA: Accurately storing health records helps you implement security controls for proper data protection.
- ISO 27001: Classifying information according to value and sensitivity helps you meet requirements for preventing unauthorized disclosure or modification.
- NIST SP 800-53: Categorizing data helps federal agencies properly structure and manage their IT systems.
- PCI DSS: Sensitivity data classification helps you identify and secure payment card information.
- CMMC: US government contactors can establish control over both personal sensitive data and CUI.
Other Benefits
In addition, a solid data discovery and data classification system can:
- Enable faster and more accurate legal discovery.
- Improve user productivity and decision-making through more effective search.
- Reduce data maintenance and storage costs by identifying duplicate and stale data.
Tips for Justifying a Data Classification Policy
In addition to outlining the data security, compliance and other benefits of data classification, here are some tips to get support for implementing your program.
Demonstrate Current Risk
The most compelling way to secure funding for a data classification program is a demo. Pick one of your data repositories, such as SharePoint, and scan it with a data classification tool. Most likely, it’ll pinpoint loads of sensitive data that needs to be tagged and properly secured. Be sure to show how many individuals have access to the data — and how many of them should not have that access.
Quantify Potential Damage
Try to quantify the damage that the organization could suffer if an adversary used a compromised account to steal data that should have been out of reach or to deploy ransomware to encrypt it.
Also list any compliance regulations the current situation might be violating, and the penalties that could be levied.
Show Additional Benefits
Classifying data can enhance the value of existing investments, like data loss prevention and user and entity behavior analytics (UEBA) tools, by identifying the most critical files to protect.
Data classification can also accelerate high-profile programs like cloud migration. Indeed, one of the biggest hindrances to cloud adoption is the fear of losing control of sensitive data. But if your files are classified, it is easy to ensure that critical content remains in secure locations.
Present a Comprehensive Data Classification Policy
Having a detailed data classification policy helps demonstrate that the project is not just worthwhile, but clearly thought out and ready to implement. Effective classification policies should:
- Use language and formatting that is clear and simple.
- Explain the purpose and scope of the data classification process.
- Detail an appropriate number of classification levels (often 3–5), with unambiguous criteria that are generic enough to apply to different data sets.
- Identify roles and responsibilities, including points of contact for clarification.
- Include a history of revisions.
How to Select a Data Classification Solution
To find the best data classification solution for your organization, be sure to look for the following capabilities:
- Automation: It’s essential to choose a solution that automates the work of classifying data at the time of creation — as well as classifying all the organization has already amassed, which can be terabytes of data.
- Compound term search: This feature improves the accuracy of determining whether a given file falls into a particular category, minimizing both false positives and false negatives.
- Index: It’s important to be able to identify sensitive terms without re-crawling the data.
- Flexible taxonomy manager: Your organization can start with out-of-the-box taxonomies, but you will soon want to add and modify terms and rules, so look for a solution that makes the task easy.
- Workflows: It’s extremely helpful to have a solution that can take specific actions automatically based on a document’s classification. For example, if sensitive data is discovered on a public share, the solution could immediately move it to a secure quarantine area.
- Breadth of coverage: Be sure the solution supports all your data sources, including structured and unstructured data in the cloud and on premises.
Conclusion: Is Data Classification Worth the Effort?
Given that an estimated 33 billion data records will be stolen in 2023, organizations are eager to improve data security. And with data privacy regulations packing steep penalties, they cannot afford to neglect compliance.
But how can you even begin to protect your most sensitive data if you don’t know where it is? And how can you get the most value from your current security tools if they can’t tell what’s inside your files?
Data classification is a foundational technology that helps you strengthen both security and compliance. Moreover, it can improve user productivity and effectiveness, speed initiatives like cloud migration, and reduce data management and storage costs. By choosing the right data classification solution, you can gain a wealth of benefits without disrupting your operations.
How Can Netwrix Help?
The Netwrix Data classification software will help you lock down critical data. But that’s not all. In addition, it empowers you to:
- Focus your security efforts on truly sensitive data.
- Ensure high-accuracy classification results with our unique compound term processing and statistical analysis technology.
- Protect sensitive files by automatically moving them to a safe area and removing permissions from global access groups.
- Embed classification information right into the files to improve the accuracy of your DLP or IRM products and streamline data management tasks.
- Reduce the cost and effort associated with the flow of DSAR requests.
To experience all advantages of Netwrix Data classification software, please visit this page.
FAQ
What is the purpose of data classification?
Data classification sorts data into categories based on its value and sensitivity.
Why is data classification important, and what benefits does it offer?
Data classification helps you improve data security and regulatory compliance. You can prioritize your protection efforts, improve user productivity and decision-making, and reduce costs by eliminating unneeded data to free up storage.
What are common data classification levels?
Data is often classified as Public, Proprietary, Confidential or Sensitive.
What software should I use for data classification?
Look for data classification software that:
- Uses compound word search to ensure accurate classification
- Has an index to find sensitive terms without re-crawling your data stores
- Includes a flexible taxonomy manager that empowers you to customize your classification parameters
- Provides workflows to automate processes such as moving sensitive data from public shares
- Supports both on-premises and cloud content sources, including structured and unstructured data
Who is responsible for data classification in an organization?
Organizations typically designate a security and risk manager, a data protection manager, a compliance committee, or a similar entity.