Microsoft Active Directory serves as a centralized point for the administration, authorization and authentication. In AD, access to network resources is granted to security principals, such as user accounts and computer accounts, and those permissions can change over time. To simplify access management and improve security, medium and large companies often use Active Directory security groups, which can contain user accounts, computer accounts and other groups. They often also use distribution groups to manage email distribution lists. Both security and distribution groups have unique security identifiers (SIDs) and globally unique identifiers (GUIDs).
The ADUC MMC snap-in is great for managing both types of groups, but PowerShell is a much more efficient way to manage them in bulk.
If you’re not already familiar with AD groups and group management, please read the Active Directory Group Management Best Practice guide before you move on.
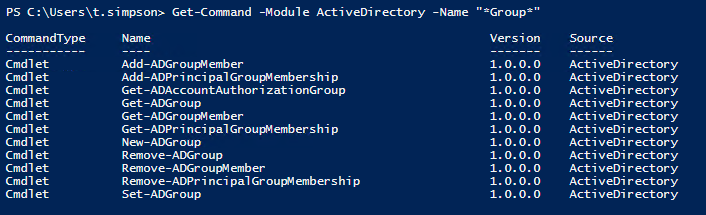
Also, keep in mind that in order to use these PowerShell scripts, you must import the module for interacting with AD — the Active Directory Module for Microsoft Windows PowerShell. This module was introduced in Windows Server 2008 R2 and is enabled by default in Windows Server 2012 and later. You can get the full list of AD module cmdlets by running the following command:
Get-Command -Module ActiveDirectory
The full list contains 147 cmdlets; however, only these eleven are related to Active Directory groups:
- Add-ADGroupMember
- Add-ADPrincipalGroupMembership
- Get-ADAccountAuthorizationGroup
- Get-ADGroup
- Get-ADGroupMember
- Get-ADPrincipalGroupMembership
- New-ADGroup
- Remove-ADGroup
- Remove-ADGroupMember
- Remove-ADPrincipalGroupMembership
- Set-ADGroup
Creating an Active Directory Group with PowerShell
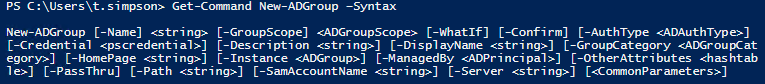
To create an AD group, use the New-ADGroup cmdlet. You can get its syntax by running the following command:
Get-Command New-ADGroup –Syntax
The easiest way to create a group is to run this short script:
New-ADGroup "Group Name"
The system will ask you to specify the “GroupScope” parameter, and then it will create a new group. However, this group will have default values, such as:
- It will be created in the default LDAP container called “Users”.
- It will have the “Security” group type.
- The members, member of, description, email and notes fields will all be blank.
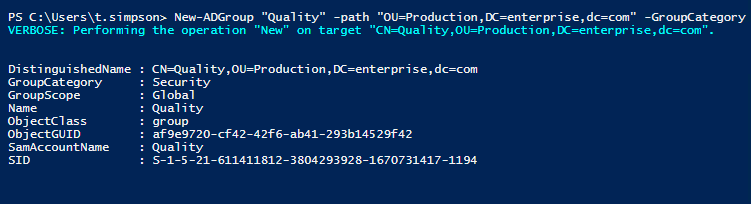
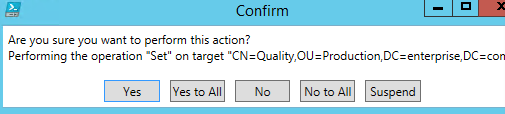
Let’s imagine that we want to create a security group called “Quality” on our AD DC. Let’s use the following parameters: It should be in the “Production” OU (-Path), it should be a security group (-GroupCategory), and it should be global (-GroupScope).
New-ADGroup "Quality" -Path "OU=Production,DC=enterprise,dc=com" -GroupCategory Security -GroupScope Global -PassThru –Verbose
If you want to make a universal distribution group, simply change the –GroupCategory parameter to “Distribution” and the –GroupScope parameter to “Universal.” You can also change the LDAP path by changing the –Path parameter.
Deleting an Active Directory Group with PowerShell
To delete an AD group, use the Remove-ADGroup cmdlet. The easiest script for that will look like this:
Remove-ADGroup -Identity Quality
You’ll be prompted to confirm the deletion of the group.
Adding Users and Computers to a Group with PowerShell
You can add users to an AD group with the Add-AdGroupMember cmdlet. For instance, if you needed to add two users, B.Jackson and E.Franklin, to the “Quality” group, here is what the script would look like:
Add-AdGroupMember -Identity Quality -Members B.Jackson, E.Franklin
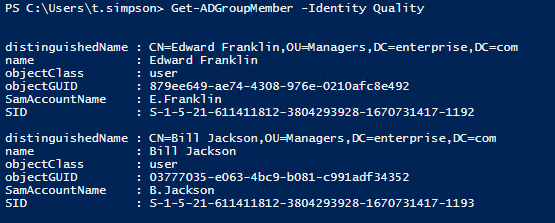
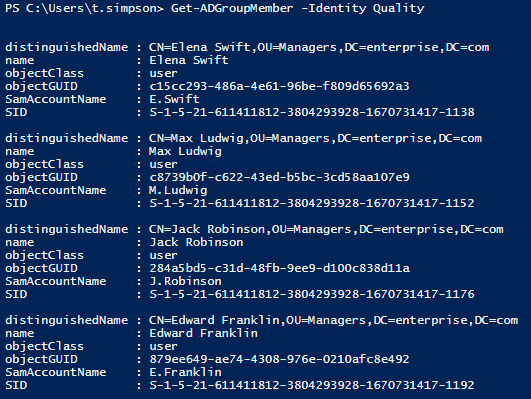
Once you’ve added users to a security group, you can run the script below to verify that they are listed as members:
Get-ADGroupMember -Identity Quality
If you need to add users to another security or distribution group, such as “Domain Admins”, specify “Domain Admins” as the value for the –Identity parameter. If you need one group to be a member of another, specify a group name as the value for the –Members parameter. The same principle applies to computer accounts, but you’ll need to append a dollar sign ($) to the end of the computer account name. For example, to add the computer “WKS043” to a group, specify “WKS043$” as the value for the –Member parameter:
Add-AdGroupMember -Identity Quality -Members WKS043$
Adding a User to Multiple Groups
To add a user to multiple groups at once, run the following script.
"Managers","Quality" | Add-ADGroupMember -Members ` (Read-Host -Prompt "Enter User Name")
You’ll be prompted to input the username.
Adding Users to a Group from a CSV file
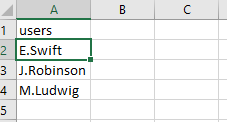
If you want to add a large number of users to a group, you can specify them in a CSV file and then import that file. Note that the list of the usernames in the CSV file must contain the SamAccountNames in the “users” column, as shown below:
To add users to group from a CSV file, run the following PowerShell script:
Import-CSV C:scriptsusers.csv -Header users | ForEach-Object {Add-AdGroupMember -Identity "Quality" -members $_.users}
Copying Users from one Group to Another
If you want to copy all members from one group to another group, run the following script:
Get-ADGroupMember “Quality” | Get-ADUser | ForEach-Object {Add-ADGroupMember -Identity “QualityControl” -Members $_}
Removing Users or Computers from a Group
To remove a user from a group, use the Remove-ADGroupMember cmdlet:
Remove-ADGroupMember -Identity Quality -Members J.Robinson
To remove a computer account from a group, specify the computer name with a dollar sign ($) at the end for the value of the -Members parameter.
Removing Multiple User Accounts from a Group
An easy way to remove multiple users from an AD group is to create a CSV file with the list of usernames and then remove those users from the group object using this script:
Import-CSV C:scriptsusers.csv -Header users | ForEach-Object {Remove-ADGroupMember -Identity "Quality" -members $_.users}
Removing a User from All Groups
To remove a user from all groups, run this script:
Get-ADUser -Identity E.Franklin -Properties MemberOf | ForEach-Object {
$_.MemberOf | Remove-ADGroupMember -Members $_.DistinguishedName -Confirm:$false
}
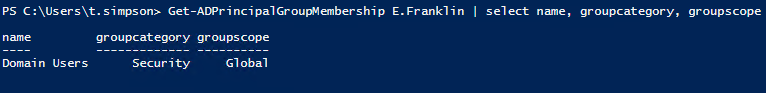
Note that the user will lose all group membership except “Domain Users”, which can be removed manually if needed.
Reporting on Active Directory Groups
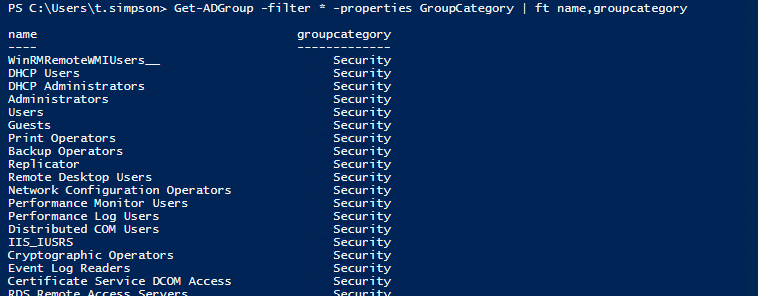
Now that we know how to perform many common Active Directory management tasks related to groups using PowerShell, let’s see how to report on what groups exist in AD:
To list all groups in AD, use the script below:
Get-ADGroup -filter * -properties GroupCategory | ft name,groupcategory
Of course, you’ll also want to review AD group members and AD group membership changes. Here are links to instructions for performing those more complex tasks:
- How to Monitor Active Directory Group Membership Changes
- How to Get AD User Group Membership Reports
- How to Export Members of a Particular AD Group
- Managing OUs and Moving Their Objects with PowerShell
Conclusion
Now that you’ve learned how to manage groups and group membership in Active Directory using PowerShell scripts, try performing some of the group management task yourself. However, be careful, and don’t forget to enable the Active Directory Recycle Bin feature so you can easily roll back your changes if something goes wrong. Remember, the ADUC MMC snap-in is great for managing groups and group membership, but PowerShell is much better for managing groups in bulk.