Originally published April, 2018 and updated June, 2019
The General Data Protection Regulation (GDPR) is a global standard designed to codify and extend the rights of data subjects. It came into force on May 25, 2018, replacing the European Data Protection Directive 95/46/EC (DPD) effective now. Fines for GDPR compliance failures can reach 20 million euros or more — substantially more than for violations of other standards, such as HIPAA, SOX and GLBA.
A key reason that businesses are anxious about this regulation is one of the GDPR breach notification requirements specified in Articles 33–34: Organizations have only 72 hours to report a breach to data protection authorities.
But there’s no need to panic. In this blog post, I answer the top 7 questions about this requirement to help you get proper processes in place or make sure that you’ve got all the processes you need. Then I’ll reveal 7 best practices for preparing an effective data breach response plan. Last, I’ll review three recent high-profile data breach cases and see how proper breach notification was sorely lacking in each.
Frequently asked questions about the GDPR’s data breach notification requirements
1. What counts as a “personal data breach”?
According to Article 4 of the GDPR, a personal data breach is a breach of security that leads to the accidental or unlawful destruction, loss, alteration, unauthorized disclosure or access to personal data stored, transmitted or otherwise processed by the organization. This also includes incidents that result in personal data being only temporarily lost or unavailable. It’s critical to understand that this definition differs dramatically from those in other standards, such as HIPAA, which often limit the concept of data breach to unauthorized access and disclosure only.
Moreover, the GDPR protects a much broader set of data. According to Article 4, “personal data” means any information related to an identified or identifiable natural person (data subject), which includes not only names and personal identification numbers, but also location data, ethnic origin, political opinions, genetic and biometric data, and much more. In contrast, most U.S. compliance standards (e.g., PCI DSS and FISMA) protect only information that can be used to commit identity theft or fraud — typically, an individual’s name and a second piece of data like their Social Security number or payment card number.
2. Who are data processors and data controllers?
To comply with the GDPR, the first thing you need to do is to determine if your company is a data processor, a data controller or both. Both roles have responsibilities for protecting personal data, but the data controller is the one who defines the procedures and purpose of data usage, while the data processor processes the data according to the rules set by controller.
A company can be a controller for some personal data and a processor for other data. However, it’s not possible to be a processor and a controller for the same data having the same processing purposes.
The Handbook on European Data Protection Law gives the following example: “The Everready company specialises in data processing for the administration of human resource data for other companies. In this function, Everready is a processor. Where Everready processes the data of its own employees, however, it is the controller of data processing operations for the purpose of fulfilling its obligation as an employer.”
When a personal data breach has occurred, you need to estimate the risks to people’s rights and freedoms. If it’s likely that there will be a risk, then you must notify the regulators; if it’s unlikely then you don’t have to report it.
Assessing the risks involves determining whether there will be negative consequences for individuals. Recital 85 explains that a breach can have various adverse effects on individuals, such as damage to reputation, physical and material damage, and other significant ill effects. If you decide not to inform regulators, you need to be able to justify your decision and prove those risks are unlikely to happen.
If the data breach poses a high risk for individuals, they should all be informed. There are the following exceptions:
- You have put into place effective protection measures like encryption or other measures that ensure that the risks “to the rights and freedoms” are no longer likely to happen.
- The controller has taken measures to stop that risks from happening after the controller became aware of the data breach.
- The data breach notifications would involve “disproportionate effort.” In such cases, a public communication, such as a press release to a prominent media organization, could replace individual notifications.
4. What are the procedures for data breach notification?
The data breach notification process depends on whether your organization is a data processor or a data controller.
When a data processor detects a data breach that puts data privacy at risk, a 72-hour countdown starts. Within these hours, data processors need to notify data controllers, and then data controllers have a communication duty to notify supervisory authorities. It’s important to understand when this period starts. For example, if you find a cybersecurity gap, you need to check whether personal data is safe. As soon as you establish that it’s not, the countdown starts. Controllers can notify the supervisors at this step that more investigation is required and that this process might take more than 72 hours, which is allowed under the GDPR. If there is a delay in notification, the data breach description should detail the reasons for it.
In addition, if a personal data breach “is likely to result in a high risk to the rights and freedoms of individuals,” the data controller must notify those individuals “without undue delay.” This is explained in GDPR Articles 33 and 34. This is a tough deadline to meet — other standards typically mandate 30–45 days for breach notification. For example, HIPAA specifies 60 days and FISMA is stricter at 30 days, while standards like SOX and FERPA do not even have a specific breach notification deadline.
Beyond these strict obligations, it’s essential to know which supervisory authority to notify. EU countries each have their local data protection authorities. If a breach affects multiple entities in Europe, the data controller should notify the lead data protection authority. The same applies for the event of a breach involving cross-border processing. The WP29 guidelines explain that in this case, notification should also be made to the lead supervisory authority, “which is not necessarily where the affected data subjects are located, or indeed where the breach has taken place.”
5. What should a data breach notification include?
Like many other compliance standards, the GDPR does not specify an exact format for data breach notifications. However, Article 33 requires notifications to supervisory authorities to include the following information:
- The nature of a data breach, the categories and approximate number of data subjects affected, and the data records involved
- The likely consequences of the personal data breach
- The measures taken or proposed to address the breach
- The name and contact details of data protection officer (DPO) or other point of contact
Affected data subjects must also be notified in an effective manner, such as through email or by posting the notice letter on the company’s official website.
6. How high are the fines for non-compliance?
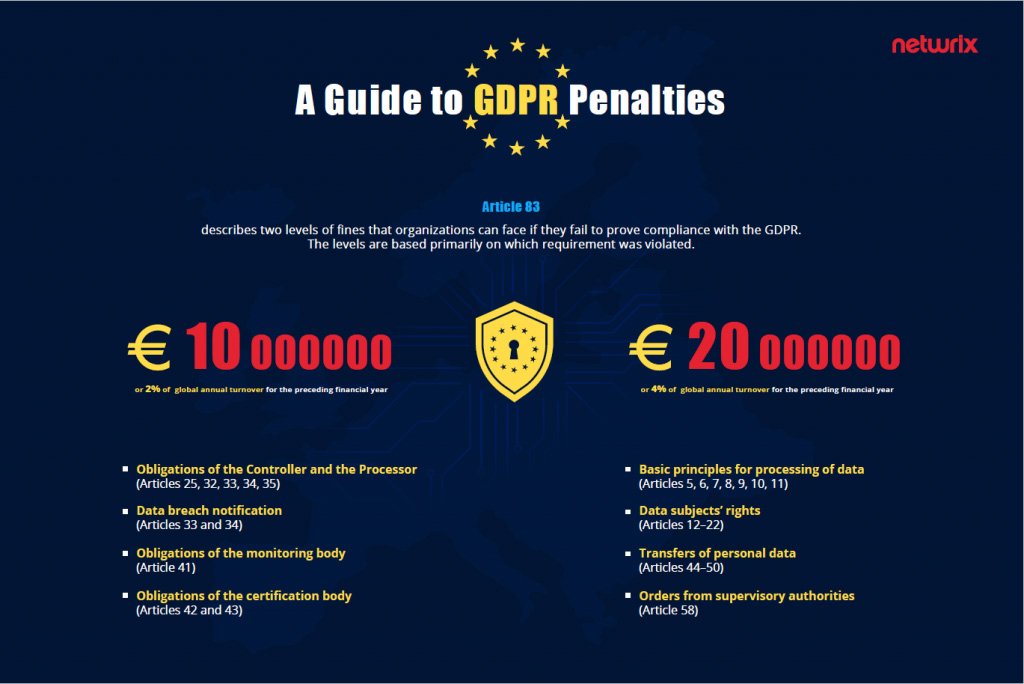
Article 83 specifies the penalties for violations of the GDPR. In particular, any violation of the data breach notification provisions (such a failure to report a data breach on time, provide a detailed description of a problem, or specify the measures that the organization will take) can cost the organization 10 million euros or 2% of their global annual turnover for the preceding financial year, whichever is greater.
7. Are there any other consequences on top of the fines?
Apart from imposing administrative fines, competent supervisory authorities have the right to issue warnings and reprimands, force organizations to report breaches to data subjects, and — in extreme cases — ban them from processing personal data (Article 58). However, there is a little chance that supervisory authorities will impose the maximum penalty for every security incident. As long as an organization cooperates with the investigation and demonstrates that it is working hard to improve security, they will probably avoid huge penalties.
Best practices for establishing a GDPR data breach notification plan
To handle data breaches in accordance with GDPR rules, you need to make sure you have all the necessary controls in place to detect, report and investigate personal data breaches. The following recommendations will help you on your way:
- Know your data well. It is essential to document what personal information you hold, where it resides, where it came from, whom you share it with and your purpose in processing it, as stated in the Articles 13 and 14. Make sure that all regulated data is stored in a secure location according to its value and sensitivity.
- Tighten access controls around data. Update access rights to make sure that protected information is available only to authorized personnel and only on a need-to-know basis.
- Stay on top of suspicious events. Enable continuous security monitoring and alerting to receive the latest information about what’s going on in your critical systems so you are better able to stop attacks in their tracks.
- Get ready for investigations. Make sure you can determine whether personal data was compromised and, if so, to take remedial action and notify all affected parties and regulatory bodies as required.
- Identify procedures to mitigate the incident. Taking steps to mitigate the negative consequences of the breach might even eliminate the need to notify authorities or data subjects.
- Document a notification procedure. Regulators assume that 72 hours is enough to report a breach for those companies that are prepared and have an incident response plan. There is no standard template, but it’s important to know which data protection authority your company needs to report and ensure you can document all the facts relating to a breach and which remedial actions have been taken. It’s also important to think in advance about how you want to communicate breaches to the individuals affected.
- Learn from your experience. It’s important to understand the reasons for a security incident so you can help prevent similar incidents from happening in the future. Review your security policy based on what you’ve learnt about the root cause of an incident, tighten your controls, and bridge any security gaps that allowed an incident to happen. Moreover, regularly conduct risk assessments and train personnel to raise their cybersecurity awareness.
Case studies: Three recent data breach notification failures
Research indicates that failure to report data breaches in a timely manner is often due to insufficient security controls and improper management decisions. C-level executives choose to conceal the breach to avoid heavy fines and reputational damage, neglecting the interests of the people who entrusted sensitive data to them and deserve to be notified if that data is compromised. The GDPR codifies and extends the rights of data subjects, so it is forcing these executives to rethink their response or face harsher financial and legal consequences.
Here are three stories of companies that failed to ensure security of their clients’ data and promptly notify relevant parties about data breaches. In all three cases, organizations knew about security incidents long before they decided to report them — making a bad situation even worse. With the GDPR now in force, similar behavior can easily result in a fine of 10 million euros or more.
1. Uber: Company pays off hackers to hide the theft of 57 million user records.

What happened?
In October 2016, hackers stole the personal data of 57 million Uber customers and drivers. The company’s CEO, Travis Kalanick, learned about the breach in November 2016, a month after a breach happened — but the company failed to provide disclosure of the breach until a year later. Moreover, the company actually paid the hackers $100,000 to delete the data and keep the breach quiet. Uber said it believes the information was never used but declined to disclose the identities of the attackers.
What data was stolen?
Compromised data included the names, email addresses, phone numbers and other personal data of 57 million Uber passengers and drivers worldwide.
What was the result of the data breach?
Uber’s security officer, Joe Sullivan, was fired. Kalanick was forced out in June 2017, although he remains a board member. Uber is still under investigation in several countries (including the U.S., the UK and Italy), and faces multiple lawsuits from customers and drivers around the world. The final amount of fines for compliance violations has not yet been determined.
2. Yahoo: The largest hack in history went unreported for three years.

What happened?
In September 2016, Yahoo revealed that a cyber attack had compromised 500 million of its user accounts. Then in December 2016, it admitted that an earlier data breach had affected 1 billion users, a number that was later revised to 3 billion — or every single Yahoo account that existed at the time.
That’s bad enough, but it gets worse. The first compromise took place in late 2014, and the second was even earlier, in August 2013 — yet neither was reported until late 2016. It’s not clear exactly when Yahoo learned about the breaches, but it seems likely that Yahoo executives knew about them long before they decided to disclose them.
What data was stolen?
User names, email addresses, telephone numbers, dates of birth, hashed passwords, and (in some cases) encrypted or unencrypted security questions and answers.
What was the impact of the data breach?
Yahoo was roundly criticized by members of the U.S. government and security experts for its late disclosure of the breaches and overall lax attitude towards security. Both the U.S. Securities and Exchange Commission and Congress are still conducting investigations. Yahoo was also hit with over 40 consumer class-action lawsuits. Finally, the breaches impacted Verizon’s acquisition of Yahoo in 2017: The original price of $4.83 billion was renegotiated down by $350 million and the deal was delayed by several months.
3. eBay: Data breach notification goes very, very wrong.

What happened?
In early 2014, hackers compromised the login credentials of eBay employees and used them to copy a database containing the records of 145 million users. Not only did it take the company a few months to discover the breach, but they waited two additional weeks to notify affected customers — many of whom had already learned about the breach from the news.
Moreover, when eBay finally posted a notification about the breach, they didn’t put it on their official website; instead, they first published it on a small corporate website, www.ebayinc.com. Then the company posted an unclear statement on PayPal’s site, which didn’t explain the situation and confused users, who thought their PayPal accounts might be also affected.
What data was stolen?
User names, home addresses, phone numbers, birth dates, email addresses and encrypted passwords.
What was the impact of the data breach?
The fact that hackers could easily access the personal data of eBay clients negatively impacted the company’s image and public relations. eBay faced a class action lawsuit, which was dismissed in 2015 due to lack of evidence of economic damage for customers. In June 2014, eBay’s CEO, John Donahoe, confirmed that eBay’s stock dropped by roughly 20% as a result of the data breach and shakeup of PayPal’s top management.
Conclusion
As these examples illustrate, data breach notifications need to be handled properly, especially since the GDPR came into force. You need control over what’s going on with the data you store, as well as a clear and tested plan for responding to a breach.
IT infrastructures have become more complicated, so it is more difficult than ever to track data flows and guarantee that sensitive files are not overexposed. For quick detection of data breaches and prompt reporting as required by law, you need a clear understanding of what’s going on in your IT environment. Furthermore, knowing where your sensitive data resides and who has access to it will help you determine the scope of a breach and exactly which files might have been compromised.