A wide range of privacy regulations govern how organizations collect, store and use personally identifiable information (PII). In general, companies need to ensure data confidentiality, avoid data breaches and leaks, and make sure data is not destroyed or altered in unauthorized ways.
The consequences of lost or leaked PII data are significant. Of course, the individuals involved can be harmed from resulting identity theft and associated costs. But organizations can lose in multiple ways as well: Not only can the costs of investigating the incident and repairing the damage be extensive, the company can be slapped with steep fines for non-compliance with a relevant privacy law, and customers can lose trust and leave forever.
This article explains what PII protection is and how to protect PII effectively with a data-centric security strategy.
What is PII?
PII is any type of information that can identify an individual. According to the National Institute of Standards and Technology (NIST), all of the following kinds of data could be considered PII:
- Name: An individual’s full name, maiden name, alias, or mother’s maiden name
- ID number: Social Security, passport, driver’s license, tax ID or credit card number
- Address: Email or physical mailing address
- Characteristics: Photographs, fingerprints, signature or handwriting, and other biometric data such as voice signature or facial geometry
- Linkable data: Other indirect data that links a person to one of the above categories, like employment information, medical history, date of birth or financial information
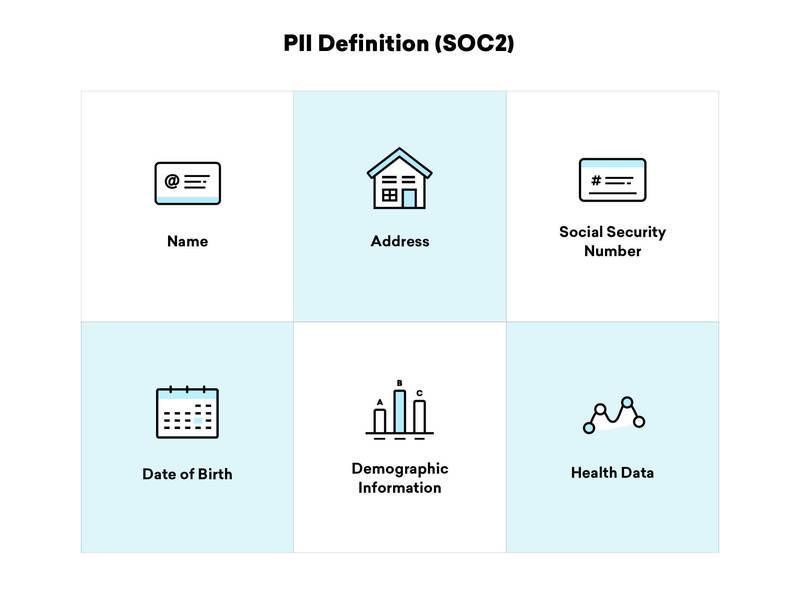
Source: Braze
It’s also important to distinguish between sensitive and non-sensitive PII, so you can create different storage and sharing plans for each type:
- Sensitive PII: Data that is not easily found from public sources, such as a person’s SSN, medical information and driver’s license number
- Non-sensitive PII: Information that is easily accessible in open public outlets like phone books and internet resources, such as a person’s zip code or date of birth.
While there are currently no federal PII protection laws in the United States, U.S. organizations are required to follow a host of other privacy laws that govern specific types of PII, including:
- Gramm-Leach-Bliley Act (GLBA): Covers customer information stored by financial institutions
- Health Insurance Portability and Accountability Act (HIPAA): Specifies standards for protecting medical records and personal health information
- Children’s Online Privacy Protection Act of 1998 (COPPA): Governs websites and online services geared toward children under 13 to protect their personal information
- Family Educational Rights and Privacy Act (FERPA): Protects educational information and related records
- Fair Credit Reporting Act (FCRA): Governs consumer information held by credit reporting agencies
- Sarbanes-Oxley Act (SOX): Protects individuals from accounting errors and fraudulent business enterprises
- California Consumer Privacy Act (CCPA): Governs the collection, sale and disclosure of the personal information of California residents
- Massachusetts data privacy law: Protects Massachusetts residents against identity theft and fraud
- The EU’s General Data Protection Regulation (GDPR): Protects the privacy of the personal data of EU citizens and impacts many companies around the globe
- Other data privacy laws, which we covered in an article about the S. data privacy approach
These regulations can be complex, so some organizations engage legal professionals to help them navigate compliance. However, it is often the responsibility of IT staff to ensure that protection practices are in place within company systems and processes.
PII protection best practices
Now that you know what PII is, let’s look at best practices for protecting it. Consider these best practices for protecting PII:
1. Discover and classify your PII. Make sure you classify your personal data into sensitive and non-sensitive categories. Where does this sensitive information currently live? Is any sensitive PII currently being stored in an insecure manner? Make sure you know exactly what data you have and where it is stored so you can implement the right security strategies for different types of data.
2. Perform risk assessments. A risk assessment helps you identify and prioritize your vulnerabilities, so you can correct the most important issues first. To perform a risk assessment, ask these key questions: Where are the gaps in your current security strategy? How do your current risks impact the sensitive data you have? What would the impact be if certain files were leaked or lost?
3. Create the right access and privilege model. Implement the least-privilege model, so that employees can access only the data they need to perform their work. A role-based access model enables you to assign certain access levels to sensitive data to protect against improper data loss or alteration.
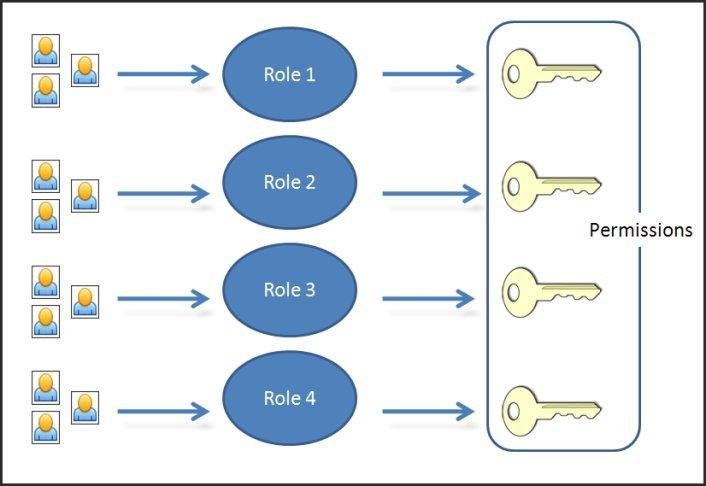
Source: Citrix
4. Use encryption. Encrypting PII helps keep it safe even if it falls into the wrong hands.
5. Don’t store PII you don’t need. Create a policy for destroying records securely when they are no longer needed. This should be a controlled process to avoid the accidental deletion of important data or leaving traces of sensitive data in unsecured locations.
6. Document your policies and procedures for handling sensitive data. Your policy should include the types of data you store, which PII is sensitive versus non-sensitive, and how different types of data must be stored and protected. Be sure to educate your users about those policies and procedures.
Conclusion
Organizations everywhere need to know what PII is and how its loss or leakage could impact their business. The data protection techniques listed above will help you identify and protect your PII. Consider investing in data security software that will help you efficiently and effectively protect your PII and monitor for security threats.
 of ENG [Free Trial] short-840x350.jpg)