Back in the early 1990s, website managers decided they needed a way to remember data about users, and the cookie was born. Browser cookies, also known as http cookies, are small text files that are deposited on your computer while you are visiting a website. Depending on your internet activity, you could have dozens or even hundreds of them stored on your computer.
These computer cookies have been a center of controversy since their introduction. Privacy advocates view them as an intrusive way for advertisers to track the activity of users and push ads and products, while website owners say they provide a convenient way for users to retain their site preferences, credentials and settings to improve their online experience.
A cookie is a tiny snippet of data or code that is stored on a web browser when a user visits a website. The cookie contains information about the person’s activity on that website, such as their preferences, login status and shopping cart contents. The next time the user visits the same website, it will recognize the cookie and ingest the stored data.
Have you ever visited an online retailer and added items to your shopping cart, only to navigate away from the site? In many cases, if you revisit the site the next day, your items will still be there so you don’t have to repeat your work. However, for better or worse, you may also be inundated by ads for the next several days promoting those items or similar products.
Another benefit of the way cookies work is that it is easier to authenticate to a website on repeat visits. That’s because the cookie stored in your browser has a unique identifier; once you’ve logged on once, the cookie remembers your login information from the previous session.
Cookies can also be used to personalize your experience by tailoring the content you receive. For instance, an online news site may suggest articles like ones you have clicked on in the past, or an online store might suggest a product that complements one of your earlier purchases.
The HTML or JavaScript code of many websites includes code snippets that instruct the user’s browser to either create a new cookie or retrieve an existing one. The website server provides the browser with the details to create a cookie, such as its name and expiration date. Other details in the cookie can include technical information about the user’s browser type and version or IP address, which ensures website optimization for each browser or computing device. Saved cookies are then used to recreate the same future user experience for the user.
- Session cookies are temporary; they are stored on a device only during the actual browsing session. They are used to maintain information while the user is accessing the site and deleted once the web browser is closed.
- Persistent cookies remain on a device even after the browser is closed. Persistent cookies have expiration dates and are deleted only then. They are used to store information for future visits, such as login credentials and other personal information that identifies the user.
- Party cookies come in two types. First-party cookies are accessed and used only by the website that created them. Third-party cookies are often used by advertising networks to track the browsing history of a user. These tracking cookies are used for things such as website analytics, targeted ad analytics and social media integration. This makes them great tools for digital marketing.
- Zombie cookies are often used by advertising networks and analytics companies to track online behavior and deliver targeted ads. They are sometimes referred to as super cookies because they are difficult to remove from a device once they are saved. Due to their more permanent nature, they are often used to create long-term profiles for unsuspecting users.
Cookies are saved in a folder on the user’s device. The location of the folder depends on the web browser that created the cookies and the operating system of the device.
While it is possible to find the cookies on your computer by using a file navigation tool like Microsoft’s File Explorer, it is a not generally a good idea to delete or modify them this way, since doing so can create issues with the websites and services that rely on them. Instead, use the cookie management functionality within the browser, as described below.
In general, browser cookies are safe. They cannot infect your computer with things like viruses, malware or ransomware, so an antivirus application will not flag the cookies on your system. However, zombie cookies or third-party tracking cookies can be targeted by some spyware applications. After all, these cookies allow others to spy on you.
Cookies can also present privacy problems for devices used by multiple users, such as when family members share a laptop or a single classroom computer serves many students. Because there may be no way to differentiate between the content for different individuals, one user may gain access to the personal information of someone else who uses the device.
In addition, cookies can be manipulated by experienced threat actors. For instance, an attacker could steal a cookie and use it to impersonate someone else on a website and log on to their account. Cookies can be used to perform cross-site scripting (XSS) attacks and to execute malicious code on the machine of a user visiting the website.
A growing number of government regulations now include requirements for cookies. For instance, the GDPR requires organizations to obtain a user’s consent before using cookies to collect their personal data. How can I prevent my browser from storing cookies?
All the major browsers make it easy to clear your cookies. Here are the steps for Microsoft Edge and Google Chrome.
Microsoft Edge
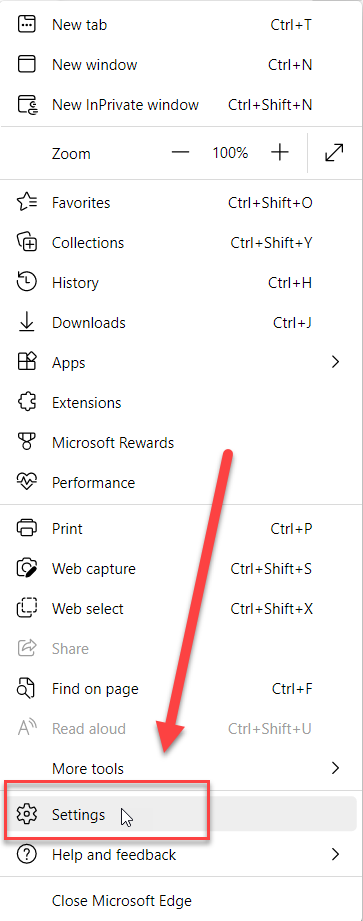
Click on the three dots (…)in the upper-right corner of the browser window and select Settings:
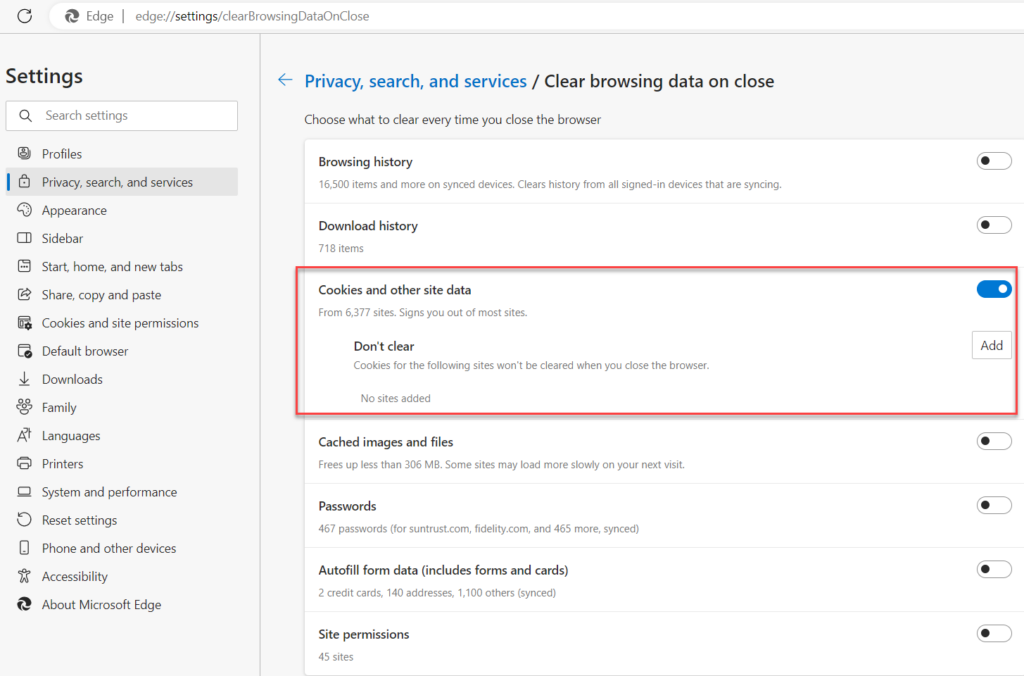
On the Settings page, select Privacy, search, and services and scroll down to Clear Browsing Data. Then choose which data you want to clear:
Google Chrome
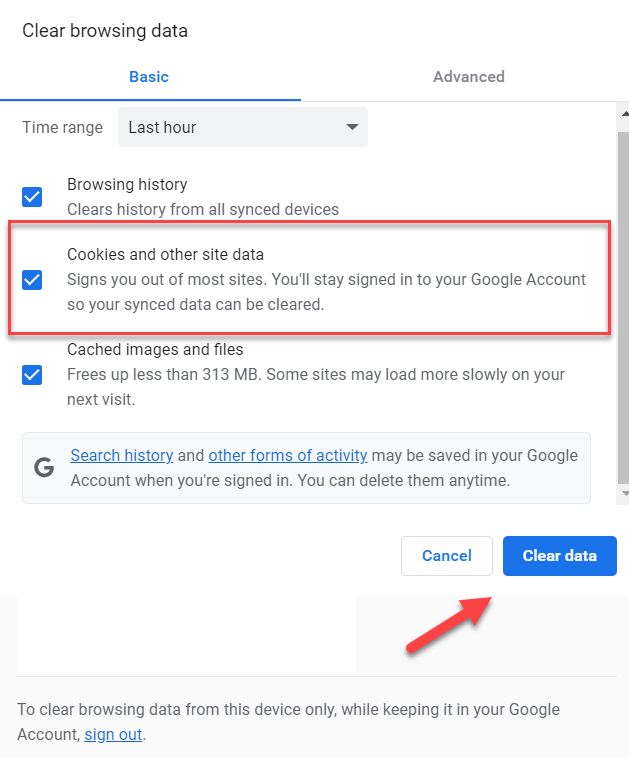
If you use the Chrome browser, click on the three dots (…) in the upper-right corner and select Settings. In the Settings window, select Privacy and Security, scroll down to Clear browsing data and select the Cookies and other site data checkbox:
If you want to avoid browser cookies on a case-by-case basis, consider these options:
- Use Incognito Mode when using your web browser. This mode will prevent search history and cookies from sticking to your computer.
- Use a proxy server to keep your identity anonymous; all requests will go through the proxy server rather than directly to the website. Proxy servers can be configured to block or remove cookies by removing the cookie header from a request before forwarding it to the website.
- Install one of the many browser extensions available on the market today that will help you manage or stop cookies.
Alternatively, you disable the use of cookies altogether in the browser’s settings. Here are the steps for Edge and Chrome.
Microsoft Edge
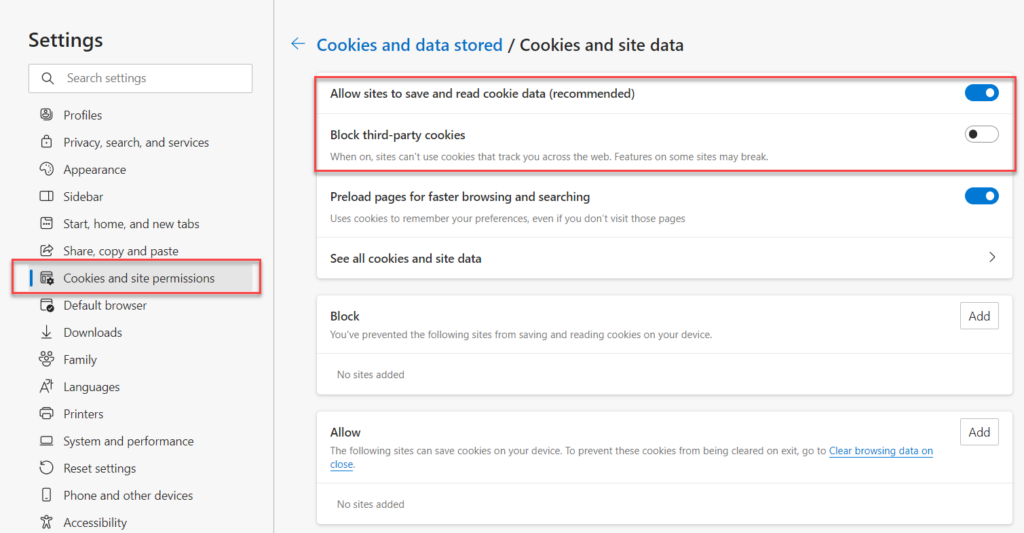
Navigate to Settings > Cookies and site permissions and specify your preferred cookie management settings:
Chrome
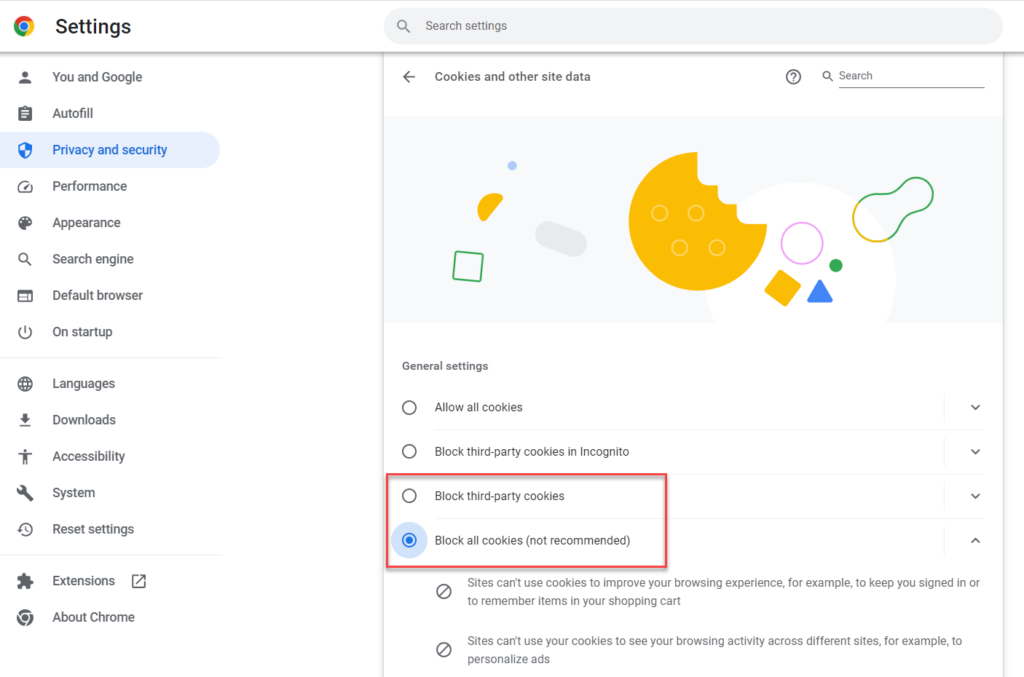
Navigate to the Privacy and Security settings screen, where you can choose to block all cookies or just third-party cookies:
Conclusion
Now that you understand how cookies work, the benefits they offer and the risks they entail, you can make informed decisions about how you want to manage them on your browsers. Of course, if you change your mind about any of the settings described here, you can easily modify your preferences.
FAQ
For iPhone users, open Settings > Safari > Clear History and Website Data to remove all cookies and browsing data. For more selective control, go to Settings > Safari > Advanced > Website Data to view and delete cookies from specific sites. On Android devices, open Chrome, tap the three dots menu, go to Settings > Privacy and Security > Clear browsing data, then select “Cookies and site data” and your desired time range. Most mobile browsers also offer incognito or private browsing modes that don’t save cookies after the session ends. Understanding mobile cookie management is crucial for maintaining privacy and security, especially when accessing sensitive corporate data from personal devices. Data security that starts with identity means controlling how your credentials and access patterns are tracked across all your devices.
Browser cookies can expose organizations to several security risks such as session hijacking, cross-site scripting (XSS) attacks, and unauthorized user tracking. The most serious threats involve session cookies being intercepted on unsecured networks, allowing attackers to impersonate legitimate users and access sensitive systems. Third-party tracking cookies create privacy risks by building detailed profiles of user behavior across multiple websites, potentially exposing business activities to competitors. Persistent cookies that store authentication tokens can become security liabilities if devices are compromised or shared. Additionally, cookies can leak sensitive information through cross-site request forgery (CSRF) attacks, where malicious sites trick browsers into making unauthorized requests to legitimate services. Organizations must implement secure cookie policies including HTTPOnly and Secure flags, regular cookie auditing, and user education about cookie management to minimize these risks.
Chrome for business environments typically has cookies enabled by default, but administrators can control cookie behavior through Group Policy or Chrome Enterprise policies. To enable cookies manually, go to Chrome Settings > Privacy and Security > Cookies and other site data, then select “Allow all cookies” or “Block third-party cookies in Incognito mode” for balanced security. For enterprise deployments, IT administrators should configure the “DefaultCookiesSetting” policy to allow cookies while blocking potentially harmful third-party trackers. Site-specific cookie permissions can be managed through the CookiesAllowedForUrls and CookiesBlockedForUrls policies for granular control over business-critical applications. Remember that overly restrictive cookie policies can break legitimate business applications and single sign-on systems. The key is finding the right balance between security and functionality – allow cookies for your trusted business applications while blocking unnecessary tracking across the open web.
Enterprise cookie security requires a multi-layered approach combining browser policies, network controls, and user education. Start by implementing Chrome Enterprise or Microsoft Edge for Business policies that enforce secure cookie settings across your organization, including blocking third-party cookies by default and requiring secure transmission for authentication cookies. Configure your identity management systems to use HTTPOnly and Secure flags for session cookies, preventing JavaScript access and ensuring encryption in transit. Implement regular cookie auditing through security tools that monitor cookie usage patterns and identify potential risks or policy violations. Establish clear cookie policies that define which sites can set cookies, how long they’re retained, and when they should be cleared. Consider deploying privacy-focused browsers or browser extensions that provide additional cookie control for high-security environments. Most importantly, train your users to recognize cookie-related security risks and understand when to clear cookies, especially when working with sensitive data or using shared devices. Smart cookie management is part of a comprehensive identity security strategy.
Cookie-related login problems typically stem from blocked cookies, expired sessions, or browser compatibility issues that prevent authentication systems from functioning properly. Start by checking if cookies are enabled for the specific site experiencing problems – many business applications require cookies for session management and will fail silently if blocked. Clear existing cookies for the problematic site to eliminate corrupted or conflicting session data, then attempt to log in again. Verify that your browser isn’t blocking third-party cookies if the application uses federated authentication or single sign-on systems that rely on cross-domain cookie sharing. For enterprise environments, check if security software or network policies are interfering with cookie functionality, particularly on corporate networks with strict content filtering. Disable browser extensions temporarily to rule out conflicts with authentication flows. If problems persist across multiple browsers, the issue likely lies with the application’s cookie configuration rather than browser settings. Document specific error messages and browser console outputs to help IT support diagnose server-side cookie policy misconfigurations. Remember that identity-based security depends on reliable session management, so cookie issues can cascade into broader access problems.



