The Netwrix 2018 IT Risks Report presents new research into the security threats organizations are facing and the actions they are taking to minimize IT risks. The report explores six IT risks: physical damage, intellectual property theft, data loss, data breaches, system disruptions and compliance penalties.
41% of companies named data breaches as the most critical of these risks. So, in this post, we decided to explore what companies view as the main causes of data breaches, who they think poses the biggest risk to data security and what measures they take to reduce their risk of a data breach. Here are some of the most interesting results.
Insiders, not hackers, are seen as the top threat actors.
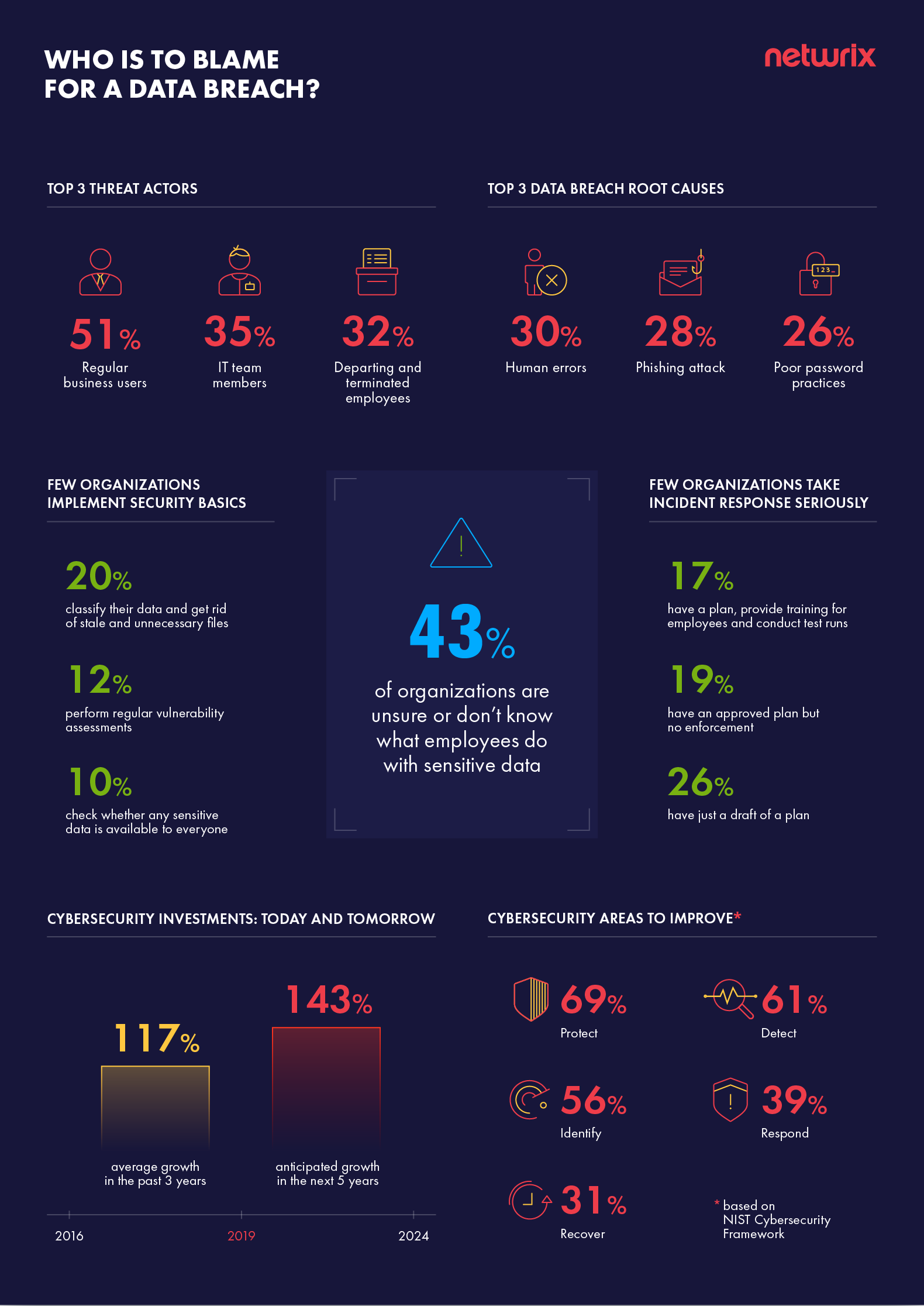
We asked our respondents who causes security incidents. Insiders took 3 of the top 4 spots in the results: regular business users (named by 51% of respondents), IT team members (35%) and departing employees (32%).
Hackers rounded out the top 4, named by 33% of IT pros. But hackers often work by trying to trick employees into opening malicious attachments in phishing emails or by taking advantage of poor corporate practices like password sharing. Therefore, regular users who fail at basic cybersecurity hygiene share responsibility for successful attacks by hackers.
Various mistakes are considered the top root cause of data breaches.
We also asked about the root causes of data breaches. Human error was the top cause, named by 30% of companies. Phishing attacks were next (28%), and poor password policies (26%) took third place.
Here are a couple of stories that illustrate how each of these causes led to a real security incident:
-
Human errors: 30%
An employee at Rainbow Babies & Children’s Hospital in Cleveland, Ohio, accidentally disclosed private health information for about 840 patients. When sending an email to a group of patients suffering from the same medical condition, the employee put the recipients’ email addresses in the To field instead of the BCC field, thereby disclosing each patient’s medical information to the entire group. In response to the incident, the hospital notified the affected individuals and regulatory bodies and reeducated employees on proper procedures for handling patient privacy.
-
Phishing attacks: 28%
Dozens of employees at Wipro, a large IT services provider in India, fell victim to a phishing campaign that enabled intruders to compromise more than 100 of the company’s computer systems and use them to launch cyberattacks against customers. Evidence suggests the attack have also targeted a number of other Wipro’s competitors, including Infosys and Cognizant.
The attack is still under investigation. It is not yet clear how long the attack went undetected and exactly which companies and information were compromised.
-
Poor password practices: 26%
Citrix Systems recently announced it would regularly force all its Sharefile customers to reset their passwords. The company claimed that this new policy was not in response to an attack, but rather was designed to reduce the risk of successful “credential stuffing” — a password-guessing attack that targets people who use same passwords across different systems and websites.
However, while forcing a password reset after a security incident makes sense, requiring regular resets violates password best practices. For example, the National Institute of Standards and Technology (NIST) warns that users who are forced to constantly change their passwords tend to choose weaker passwords and update them using common transformations, such as incrementing a number in the password, that are well known to hackers. As a result, the policy tends to hurt, rather than enhance, security.
Organizations neglect security basics
Following security best practices is critical to reducing the risks of human mistakes, phishing attacks, poor password practices and other factors that lead to data breaches. However, organizations are failing to attend to security basics. Only 20% of companies use data classification and sort out stale and unnecessary files, and less than 25% perform regular vulnerability assessments and check whether any sensitive data is available to everyone.
Moreover, 43% of organizations are unsure or don’t know what employees do with sensitive data — which leaves them vulnerable to the risks coming from insiders.
Knowing who has access to your sensitive data, minimizing its exposure according to least privilege and monitoring use of that data are essential parts of any data-centric security approach. After all, when you lack true visibility into what is going on in your IT infrastructure, it’s impossible to ensure that data access is limited to authorized personnel only and those employees deal with the data in an appropriate manner. Lack of visibility prevents you from detecting security incidents in their early stages and responding promptly, which makes data breaches more likely.
Organizations are ill-prepared to respond to a security incident
Security best practices are not limited to strategies for reducing the risk of a successful attack. Organizations are advised to take an assume-breach posture, which involves ensuring they can:
- Quickly detect a data breach
- Respond to an incident in a timely manner
- Determine the scope of a breach
- Recover data, systems and services that were stolen or destroyed
However, the Netwrix report shows that only 17% of organizations have an incident response plan, provide training for employees and conduct test runs. 19% have an approved plan but never followed through on the other steps, and 26% have only a draft of a plan. This puts them at increased risk of missing a breach or handling it improperly, which can dramatically extend the impact of an incident — companies are justly criticized for being slow to inform customers when their personal data is compromised, and regulators hike compliance fines when data breach reporting requirements are not met.
Summary
Building a strong cybersecurity posture has never been an easy task, and the increasing complexity of both IT environments and the threat landscape makes it harder than ever. The good news is that companies are increasingly ready to commit to allocate budget to cybersecurity — respondents report that their cybersecurity investments grew by 117% in the past 3 years and they expect them to increase by 143% over the next 5 years. For most organizations, focusing that additional budget on security basics and implementing best practices will deliver the most value.
View the full infographics for the 2018 IT Risks Survey here: