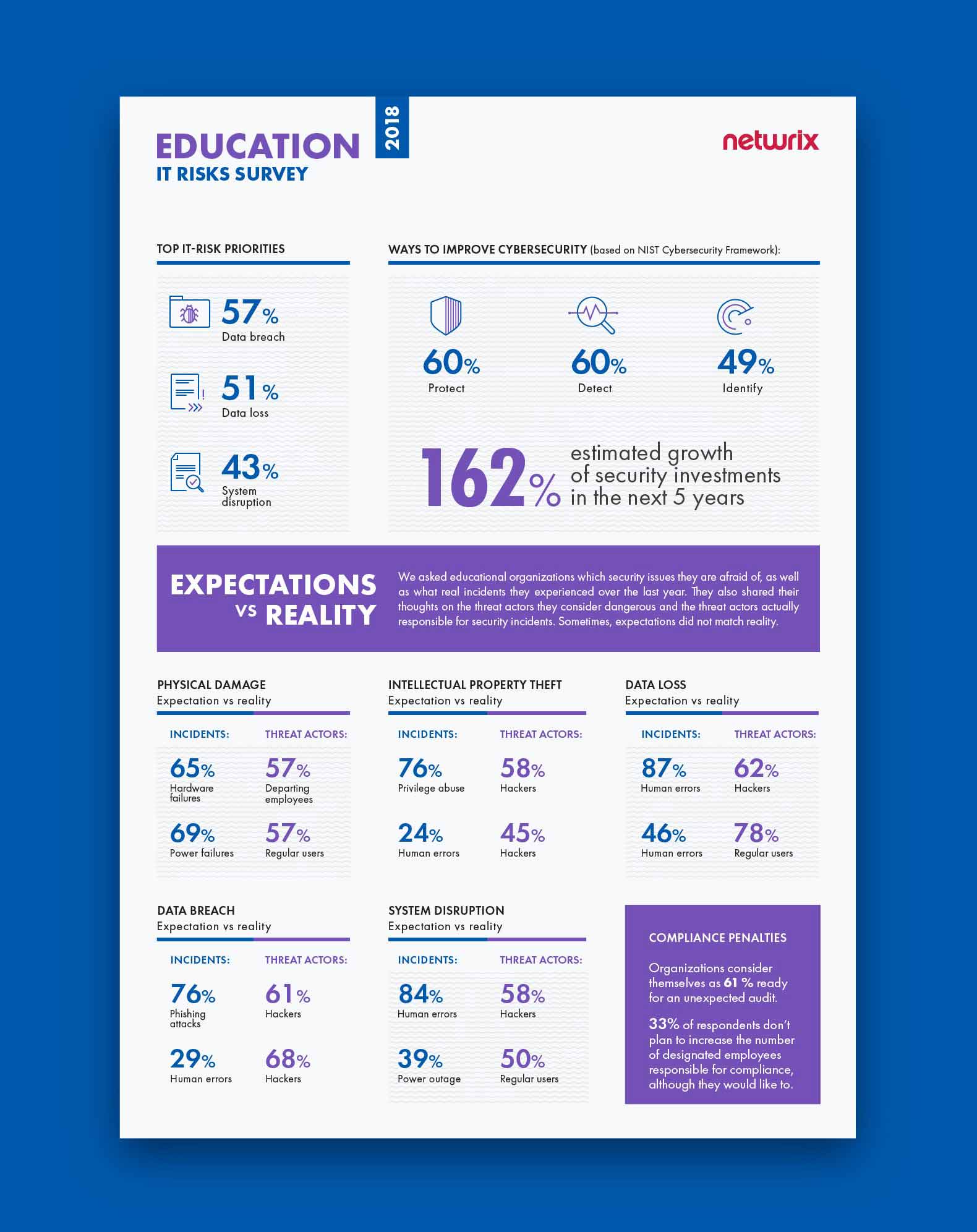
In this blog post, which is based on the results of Netwrix’s 2018 IT Risks Report, we will dive deeper into the problems that face schools, colleges, universities and other educational organizations. The survey covers the six most common types of IT risks: physical damage, intellectual property theft, data loss, data breaches, system disruption and compliance penalties. Educational organizations do not always deal with these risks effectively; sometimes, their expectations towards most dangerous security issues do not match the reality. Also, the threat actors they consider dangerous are not necessarily the ones who are responsible for real incidents involving sensitive data.
We surveyed 125 educational organizations to find out which security issues and humans pose a real threat to security of their assets and which are incorrectly assumed to be dangerous. The figures below reveal some real difficulties that educational institutions face on their way to data security, and we provide some real-life examples to support the survey results and illustrate how dangerous IT risks can be for the education sector.
Physical damage
Physical damage is any harm to an organization’s hardware assets, such as servers, laptops or network devices. In educational organizations, causes of physical damage can include an improper storage environment, careless handling and inadequate hardware maintenance. Practice shows that physical damage is not the biggest IT risk for educational organizations, since it usually doesn’t lead to catastrophic consequences in terms of financial loss or reputational damage.
The survey findings reveal that organizations are not always savvy about which causes of physical damage they need to be most afraid of. The majority of respondents said that they were concerned about hardware failures, while in reality most of the security incidents due to physical damage during the past year involved power failures (69%); hardware failures are in second place (62%). In terms of threat actors, about 57% of respondents named departing employees as their biggest threat, while in reality it’s regular business users who cause the most physical damage (also 57%); 20% named departing employees as the main actors in these real incidents, which ranks them third among all threat actors cited.
Case study: Beaverton School District suffers damage to data center from fire suppression system
In 2013, the Beaverton School District experienced several days of disruption after an errant alarm set off a fire suppression system in the district’s data center, damaging hard drives and servers. According to the chief technology officer at Beaverton School District, the incident affected all of the systems that staff needed to do their jobs: They were unable to use email or access class lists, student schedules and online textbooks. The district’s technology department worked for several days to patch and repurpose systems, and finally managed to get all the systems back online. However, the district lost all the data entered into one of its systems shortly before the incident and staff had to re-enter it.

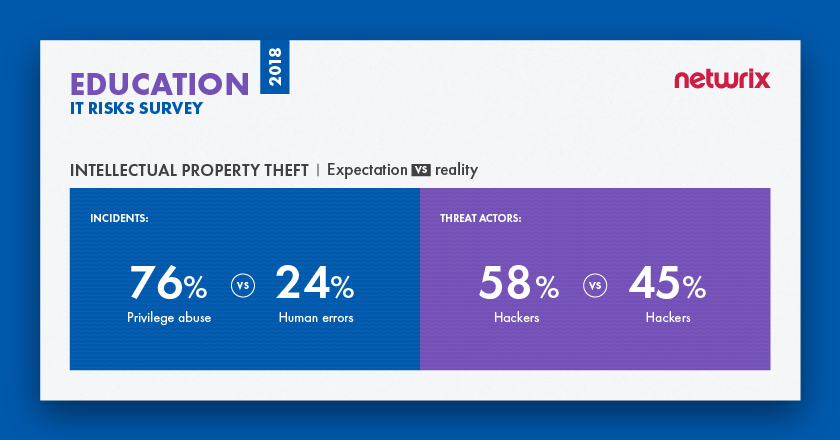
Intellectual property theft
Intellectual property theft usually involves robbing people or companies of their inventions and ideas. In the educational sector, intellectual property can include teaching plans, research results, inventions, scholarly publications, theses, presentations, software and databases. Under certain circumstances, the deliberate theft of intellectual property can be a serious IT risk for educational institutions; in particular, if a university is involved in medical, environmental or technical research, or performs a research on behalf of federal government, intellectual property theft can lead to substantial reputational damage, termination of contracts, loss of competitive advantage and financial expenses. For other educational institutions, this risk may be far less pressing. In fact, most schools and institutions encourage knowledge sharing and don’t object to making many of their publications and lectures publicly available.
According to the survey results, organizations in the education sector are often mistaken about the true causes of most IP theft incidents. The vast majority of respondents (76%) are confident that the most dangerous security issue for them is privilege abuse, while in reality the most common cause of IP theft incidents (24%) is human mistakes; privilege abuse is the third most common cause (17%). On the other hand, organizations know exactly whom they need to be afraid of. 58% of respondents named hackers as the chief threat actor in IP theft, and they are absolutely right, as hackers were involved in 45% of real IP theft incidents.
Case study: Ex-employees pay insiders to steal intellectual property from Whiteriver Unified School District
In 2017, the director of information technology at Whiteriver Unified School District received disturbing news: Another school was using exactly the same curriculum maps as Whiteriver Unified School District. After an internal investigation, it became clear that two insiders stole the teaching plan for the whole school year. They admitted that two other teachers who used to work at Whiteriver Unified School District paid them for copies of the curriculum maps so they could use them in their new positions at the neighboring school.
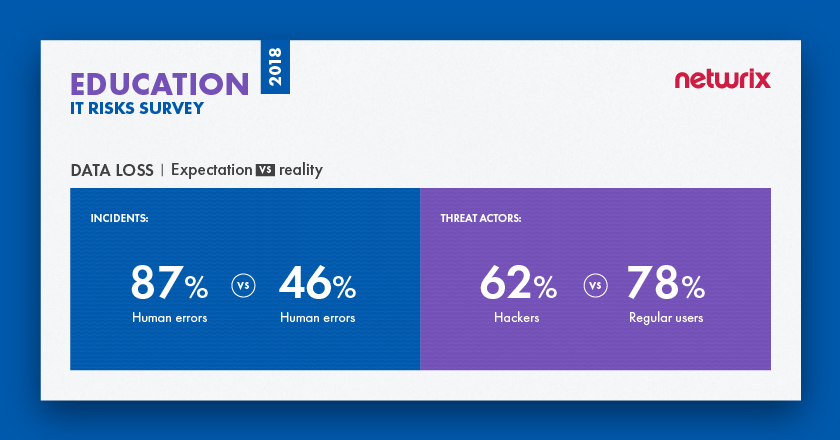
Data loss
Data loss occurs when information is destroyed by failures during storage, processing or transmission. This IT risk involves intentional damage (e.g., erasure, session hijacking, malware infiltrations and IoT exploits), as well as software failures and human mistakes. The consequences of data loss for educational organizations include reputational damage and huge costs for restoring the data. Also, if the personal or financial data of students and employees goes missing, it could get into the wrong hands and be used for phishing attacks, blackmail or fraud.
The survey shows that organizations correctly consider human errors to be the leading root cause of data loss. However, their expectations towards threat actors do not match the reality. 62% consider hackers to be the most dangerous threat actors, while in reality it’s regular users who were responsible for the most real incidents (78%). Hackers are in the second place at 37%.
Case study: A minor fire erases spring grades at Washington County Public Schools
In 2018, Washington County Public Schools reported that all spring grades of 22,000 students were permanently erased when a minor fire damaged several servers and crippled access to the online system used for grade review. The school officials admitted that the data had not been properly backed up. Most servers were restored within a week, but some data, including elementary report cards for the third marking period and all grades entered for the fourth marking period, couldn’t have been recovered. Although the school officials apologized to parents and students, they were criticized for lack of adequate communication and failure to give all the necessary details about the incident.
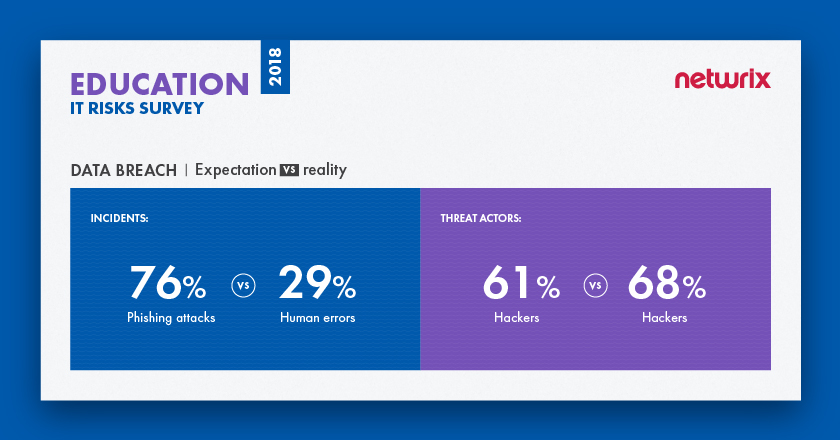
Data breach
A data breach is a confirmed security incident in which sensitive, protected or confidential data is copied, transmitted, viewed, stolen or used by an unauthorized party. Techniques for this cyber risk range from phishing and state-sponsored attacks to simple human mistakes, lost devices and misconfigured databases. Data breaches are a critical IT risk for educational organizations; consequences can include reputational damage, huge fines for non-compliance, and additional expenses for investigation and remediation of security issues. Unfortunately, educational organizations are not well prepared for data breaches due to lack of security awareness among staff and lack of resources to ensure proper data security. However, institutions that perform research on behalf of state governments usually receive more financial support and pay much more attention to protection against security threats.
76% of educational organizations say that phishing attacks are the threat pattern they need to be afraid of, while in reality, the most common cause of data breaches is human mistakes (29%)
According to the survey, 76% of organizations say that phishing attacks are the threat pattern they need to be afraid of, while in reality, the most common cause of data breaches was human mistakes (29%); phishing attacks were in second place at 27%. However, companies are quite savvy about which threat actors cause the most harm. 61% said that they are afraid of hackers more than anyone else, and hackers indeed are responsible for the most real incidents (68%).
Case study: University of Greenwich is slapped with a huge fine due to a 2016 breach
In 2016, hackers took advantage a vulnerability in an unsecured microsite of the University of Greenwich (UK). The microsite was built in 2004 specifically for a training conference; unfortunately, it was never shut down or made secure afterward. The site was initially compromised in 2013, and in 2016, hackers exploited a vulnerability in it to access other areas of the university’s web server and steal the personal data of 19,500 students and staff, such as names, addresses and telephone numbers. Around 3,500 of those records included extremely sensitive data, such as extenuating circumstances, details of learning difficulties and staff sickness records. All the data was subsequently posted online.
According to the Information Commissioner’s Office (ICO) investigation, the university was not aware that their infrastructure had a vulnerable microsite and did not properly identify risks to its IT infrastructure. In 2018, ICO fined the university £120,000 for the major data breach.
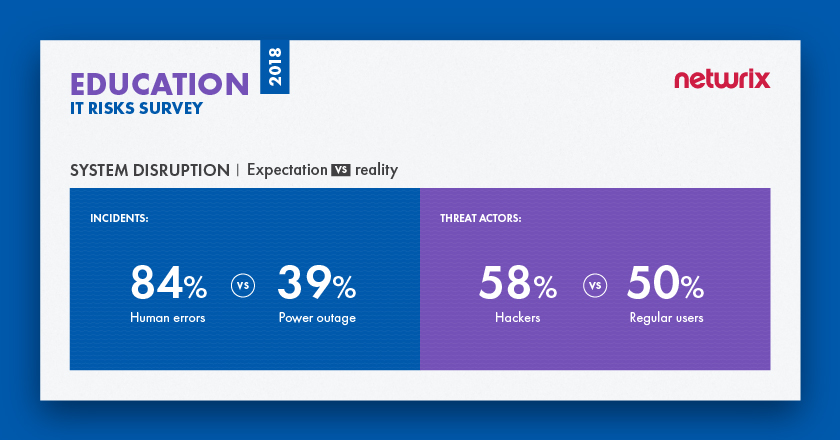
System disruption
A system disruption (or service interruption) is the inability of IT systems to perform their primary function for a period of time. Common causes of system disruption include power outages, natural disasters, malicious techniques (e.g., sabotage, DDoS attacks and ransomware), and human mistakes. This IT risk is not the most critical for educational institutions, since typically the outage can be fixed and won’t result in substantial financial losses or reputational damage.
In terms of causes of system disruption, organizations are most afraid of human errors (84%). Nevertheless, in reality, power outages are the most frequent cause (39%), and human errors are in second place (27%). Organizations think hackers are the most dangerous threat actor (58%), but this does not match reality either: Regular users are responsible for the most incidents (50%), while hackers are in third place (40%).
Case study: A computer program outage affects school districts in Washington state
In 2018, an essential computer system used by nearly every school district in the state of Washington state was down for five days. Skyward, the software system that teachers and parents use to record and monitor attendance, grades and homework assignments, was down due to a technology glitch. Skyward officials said that outage was caused by a system failure: When the Washington School Information Processing Cooperative (WSIPC), which manages Skyward and other information services, attempted to conduct a firmware upgrade of their data center, it caused an outage of WSIPC-managed services throughout the state. The outage was fully restored in five days; before that, teachers were required to use alternative methods of submitting class attendance figures, including alternative online spreadsheets and traditional paper-based submissions.
Compliance penalties
Education is a quite heavily regulated industry. On the one hand, educational organizations have to comply with specific industry standards like the Family Education Rights and Privacy Act (FERPA) and the Protection of Pupil Rights Amendment (PPRA). On the other hand, they store a great deal of sensitive personal, financial and even healthcare data, so they are often also subject to standards like HIPAA and PCI DSS. Practice shows that it can be difficult for educational organizations to prove their compliance to regulators for several reasons. First, universities often fail to consider the personal and financial records they store to be sensitive data and therefore do not adequately protect them. Second, educational institutions suffer from lack of security investments and often do not have specific people to deal with compliance. Finally, many institutions have multiple campuses and very complicated IT infrastructures, which makes it difficult to keep the systems and data under control.
Only 61% of educational organizations consider themselves ready for an unexpected compliance check, which is the lowest result among all other industries
61% of educational organizations consider themselves ready for an unexpected compliance check, which is the lowest result among all other industries. 33% of respondents don’t plan to increase the number of employees responsible for compliance, although they would like to. 27% don’t plan to increase the number of compliance-oriented employees at all.
Case study: University of Washington Medicine receives a $750 000 fine for HIPAA violations
In 2013, University of Washington Medicine (UWM) alerted the Office for Civil Rights (OCR) to a data breach that exposed the protected health information (PHI) of approximately 90,000 UWM patients. An employee fell for an email scam, which resulted in malware being installed on the healthcare provider’s computer network. This enabled hackers to obtain the PHI. The OCR investigations discovered HIPAA violations related to failing to properly conduct comprehensive risk analyses. In 2015, UWM agreed to pay $750,000 to the OCR and also agreed to an action plan to address its HIPAA failures.
Summary
The 2018 IT Risks Report shows that educational organizations do not always make the right decisions about security. Sometimes they know exactly what and who poses a real threat to their systems and data, but sometimes their expectations do not match reality. When it comes to security incidents, organizations seem to blame hardware failures, phishing and privilege abuse, while in reality human mistakes cause more security incidents. Hackers and departing employees might seem to be the biggest threat to systems and data, but in reality, it’s regular users who are involved in most security incidents.
According to the survey, data breaches are seen as the top IT risk, even though the cost of a data breach in the education section is not as big as in other industries, according to Ponemon’s 2018 Cost of Data Breach Study. Lack of security investments, lack of security awareness among staff and complex IT environments make it difficult for educational institutions to ensure security of their systems and data. To be more prepared for insider and outsider threats, educational organizations plan to increase their
security investments by 162% in the next 5 years. They see detection of unauthorized activities and protection against potential issues as the key ways to improve cybersecurity.
View the full infographics for the 2018 IT Risks Survey and the results for the education sector here:



.png)