This is the third post about the most common IT risks facing major industry sectors. This time, we have extracted data from the 2018 IT Risks Survey to find out more about the problems and concerns of banks, insurance companies, credit unions and other financial institutions. The survey covers the six most common types of IT risks: physical damage, intellectual property theft, data loss, data breaches, system disruption and compliance penalties.
Unfortunately, sometimes the expectations of financial organizations about the most dangerous cyber risks and threat actors do not match reality. Indeed, the incidents that happen in real life are not necessarily the incidents that these organizations are most worried about. The same works for threat actors: Sometimes the people responsible for real incidents are not the ones they expect. This mismatch makes it difficult for these institutions to deal with IT risks effectively
The survey includes data from 125 financial organizations. Here, we will illustrate the survey results with some real use cases from financial institutions.
Physical damage
Physical damage is any harm to an organization’s hardware assets (e.g., servers, laptops and network devices) caused by improper storage environment, inadequate hardware maintenance, natural disasters and other factors. Financial organizations are typically well prepared to minimize this IT risk — these companies work with extremely critical data and are responsible for cash flows, so they invest in the physical security of their assets.
Nevertheless, the survey results indicate that expectations about most the dangerous security incidents do not match reality. Most of organizations are afraid of human errors, but in reality, hardware failures cause most damage, with 69% of respondents reporting that hardware failures led to physical damage of equipment over the last year. Human errors ranked third, with just 37% reporting physical damage due to human error over the year. In terms of threat actors, organizations also don’t fully realize who poses the biggest threat to their systems and data. While the majority assumes it’s hackers, in reality, regular users are responsible for the most physical damage incidents (57%). Hackers are not even in top five of most dangerous threat actors — only 10% of respondents mentioned that hackers were involved in these types of incidents.
Case study: A loud noise knocks out computers that run stock exchanges across northern Europe
In April 2018, a high-decibel whistle knocked out Nasdaq servers for several hours at a DigiPlex data center in Stockholm. The noise, which came from an errant fire prevention system, caused vibrations that damaged the alignment of disk drives’ read-write heads.
No other customers were affected, but Nasdaq was forced to fly new servers in to Sweden. The incident shut down trading in the stock markets for Sweden, Denmark, Finland, Latvia, Estonia and Lithuania, as well as equity and fixed-income markets for Iceland, until the exchange operator was able to activate its backup servers.
Intellectual property theft
Financial organizations often hold intellectual property, such as bespoke tools that help them analyze and predict stock market trends. Theft of IP can lead to negative consequences, such as loss of competitive advantage and decline in revenues.
According to the survey results, financial organizations know the true cause of most IP theft perfectly well — human errors. However, their expectations towards threat actors don’t match reality. More than half of respondents said that they are afraid of hackers, while in reality, regular users are responsible for the most (45%) security incidents. Hackers take fourth place among threat actors involved in real incidents; they were mentioned by 30% of organizations.
Case study: Chicago trader steals proprietary trading secrets from his employer
Over a five-month period in late 2013 and early 2014, David J. Newman stole proprietary computer code and trading software belonging to his employer, WH Trading LLC, Chicago’s leading proprietary trading firm. Newman downloaded more than 400,000 files to multiple USB thumb drives. The stolen IP was developed by WH Trading’s mathematicians, statisticians, software developers and traders over more than 15 years “at a cost of more than $20 million,” according to the U.S. attorney involved in the case.
Newman resigned from the company in March 2014 after establishing his own trading firm, NTF LLC, through which he intended to use the stolen trade secrets to compete directly with WH Trading. In 2016, Newman pleaded guilty to one count of theft of trade secrets; he was sentenced to a year and a day in federal prison.
Data loss
Financial organizations store and process extremely sensitive data of their clients and employees, including personal data (e.g., names, ID numbers and addresses) and financial data (e.g., credit card and bank account numbers, payment records and credit history). If this information is lost or destroyed due to improper storage, intentional damage or human mistakes, it may have a lasting impact on business. Organizations may have to spend time and resources both investigating the incident and recovering the information. Data loss can also lead to service disruption, reputational damage, lawsuits from customers and even the revocation of the company’s banking license.
For financial organizations, hackers are the most dangerous threat actors, but in reality, regular users were responsible for 78% of incidents
Most organizations fear human errors as the most common cause of data loss, and indeed this is the top cause of actual data loss incidents, mentioned by 46% of respondents. In terms of threat actors, organizations delude themselves into thinking that hackers are the most dangerous threat actors, but in reality, regular users were responsible for 78% of incidents; hackers lagged behind in third place.
Case study: Australian largest bank loses backup data for 20 million accounts
In 2018, Commonwealth Bank in Australia (CBA) admitted that it lost backup data for more than 15 years of customer statements, affecting almost 20 million accounts. The lost data included customer names, addresses, account numbers and transaction details from 2000 to early 2016. These records were stored on two magnetic tapes, which were sent to a subcontractor to be destroyed in 2016 after the decommissioning of a data centre. When the bank did not receive any documentation providing evidence the tapes had actually been destroyed, it initiated an investigation to find out what had happened to the data and informed several regulatory bodies about the incident. The bank did not tell customers there was a potential problem until BuzzFeed News broke the story.
The missing tape drives were never recovered. The accounting firm said that drives most likely fell from the truck that was carrying them to be destroyed. CBA wasn’t fined for the incident, but it became the subject of a public scandal. The Australian Prudential Regulation Authority (APRA) published a report that identified a number of shortcomings in the bank’s governance, culture, and accountability frameworks, particularly in dealing with non-financial risks. The decision made by CBA not to inform its customers about the incident was described by the Australian prime minister as an “extraordinary blunder.” CBA publicly apologized to its customers and assured them that there was no data compromise.
Data breach
Major breaches have been hitting financial organizations for several years now; the examples are JP Morgan Chase, Cardsystems solutions, Korea Credit Bureau and Equifax, which is the biggest data breach in the financial industry to date. According to the 2018 Verizon Data Breach Investigations Report, personally identifiable and card payment data are the most frequent types of data compromised in data breaches, with financial gain and espionage being the key motives for culprits. Hackers see the financial industry as a tempting target; they can use stolen data directly for financial gain, sell it on the black market or use it in fraud schemes.
The consequences of a data breach in the financial sector include fines for non-compliance, legal actions, the resignation of key people, and huge expenses for security investigations and remediation. In the worst cases, a data breach can have a long impact on a company’s reputation and even result in bankruptcy. Smaller financial organizations are more vulnerable to data breaches than large organizations because their defenses are generally weaker and they have less resources to devote to strong data protection.
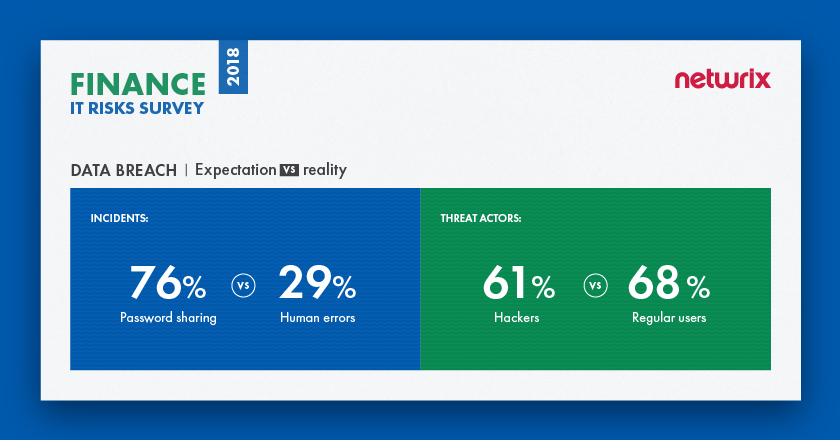
Vast majority of financial organizations (76%) consider password sharing as most critical security issue; in reality, most data breaches are caused by human errors (29%) such as unintentional disclosure or clicking on phishing linksast
The research shows that the vast majority of respondents (76%) consider password sharing as most critical security issue; in reality, however, most data breaches are caused by human errors such as unintentional disclosure or clicking on phishing links. Unsecured password sharing, as a separate pattern, takes second place among real incidents that organizations experienced over the year, mentioned by 26% of respondents. In terms of threat actors, we again see the familiar picture: Organizations think that hackers are the most dangerous, but in reality, regular users are involved in most incidents (68%). Hackers are the second biggest threat to data security (42%).
Case study: Credit reporting giant suffers one of the largest data breaches in history
In 2017, credit reporting giant Equifax reported that hackers had gained access to its credit-report databases containing data on 148 million people, including Social Security numbers, dates of birth and driver’s license numbers, as well as the credit card numbers for 209,000 people.
The U.S. Government Accountability Office (GAO) confirmed that a single web server with out-of-date software led to the breach, which went undetected for 76 days. Also, attackers accessed a database that contained unencrypted credentials that they used to access other internal databases. After discovering the breach, but before notifying the public, three Equifax senior executives sold shares in the company worth almost $1.8m.
After the breach was made public, Equifax stock dropped more than 13% in after-hours trading. The CEO, CIO and CSO of Equifax resigned. Eight state banking regulators imposed a consent order on Equifax in June, requiring security improvement, auditing, and reporting. Finally, this breach also caused several legislative initiatives: US senators Elizabeth Warren and Mark Warner introduced a bill to hold credit agencies accountable for data breaches.
System disruption
A system disruption (or service interruption) is the inability of IT systems to perform their primary function for a certain period of time. Common causes of system disruption include power outages, malicious incidents caused by insiders and outsiders (including sabotage, DDoS attacks, ransomware and other), and human mistakes. For financial organizations, this is one of the most critical IT risk, since it can negatively affect the availability of online services and make it impossible for an organization to properly serve its clients, e.g., perform financial transactions. Time is money, and even an hour of system outage can result in huge financial losses, as well as reputational damage or key people losing their jobs.
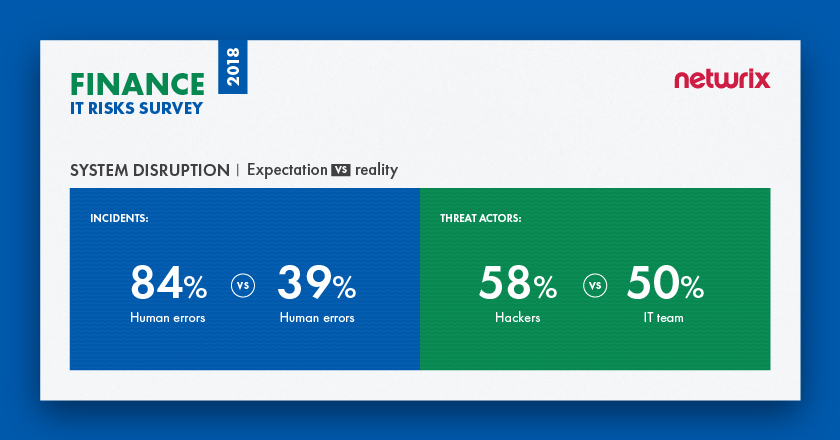
The survey revealed that financial organizations are aware of what they need to be afraid of. The majority of respondents (84%) say that human errors are most critical security issue. Indeed, human errors caused 39% of downtime incidents over the last year. However, organizations are not as savvy about threat actors: Organizations think that hackers are the biggest threat, but in reality, the most common threat actors are IT team members — 50% of organizations said that their own IT employees were involved in incidents that led to system disruption. Nevertheless, hackers are still a major threat, as they take second place among threat actors responsible for real incidents (37%).
Case study: UK bank’s CEO leaves his job due to an IT disaster
A bungled system switch at midsize bank TSB in the UK in April 2018 led to several days of outages of its online banking systems. As a result, TSB’s internet banking and mobile app services for Android and iOS were not working for UK customers. Due to a mismanaged banking platform migration, customers were left without access to their accounts for more than a week. In July 2018, TSB customers again complained that they were locked out of their online banking, which happened shortly after TSB updated its mobile app. This caused a huge scandal in social media, with customers complaining on Twitter and threatening to close their accounts with the bank.
TSB chief executive Paul Pester was criticized by Members of Parliament over his handling of the crisis, which has cost bank’s Spanish parent Sabadell (SABE.MC) more than 200 million euros (£180.3 million) and damaged TSB’s reputation. It also cost Pester his job and a £2m bonus.
Compliance penalties
Financial institutions are subject to a variety of standards, including ones that establish requirements for securing electronic financial records (such as SOX), ones that regulate the collection and use of customers’ private information by financial institutions (such as GLBA), and ones that set requirements for organizations that store and process cardholder data (e.g., PCI DSS). Although compliance penalties are not exactly an IT risk, they are still a major concern for financial organizations. For example, failure to prove compliance with PCI DSS will result in huge fines for every month the merchant is non-compliant, ranging from $5,000 to $100,000 per month. For non-compliance with GLBA, a financial institution can be fined up to $100,000 for each violation, while officers and directors can be fined up to $10,000 for each violation. Other consequences of non-compliance include suspension of licenses, legal actions and additional federal audits to make sure that you comply with the security standards.
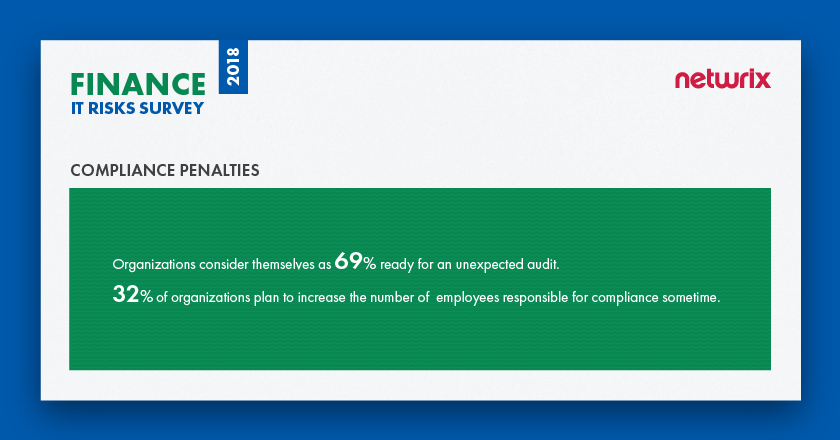
According to Netwrix’ survey, 69% of organizations consider themselves ready for unexpected compliance checks, which is slightly above the average (66%) for all industries. 32% of financial organizations plan to increase the number of employees responsible for compliance at some point.
Case study: Atlanta-based payments processor fined for compliance failure
In 2012, Atlanta-based credit and debit card processor Global Payments Inc. reported unauthorized access to its processing system dating back to at least early June 2011. The company said the affected portion of its processing system was confined to North America and at least 1.5 million payment card numbers might have been stolen by hackers.
The investigation revealed that some data may have been stolen, but that cardholder names, addresses and Social Security numbers were not obtained by the criminals. During the investigation, Global Payments CEO Paul Garcia said that the breach had already cost the processor $84.4 million and could cost an additional $25 million to $30 million in 2013. Those costs include expenses to investigate and remediate the breach, fines for non-compliance with PCI DSS, and fines from the card brands impacted by the incident.
Summary
The Netwrix survey shows that expectations about IT risk factors in the financial sector do not always match the reality. On the one hand, these institutions seem to understand that the human factor is the root cause of most incidents. On the other hand, they are often mistaken about who poses the biggest threat to their data and systems: For every IT risk, they are most afraid of hackers, while in reality their own business users and members of IT team are responsible for the most incidents.
The survey results also showed that protection against data breaches is the top IT risk priority for the majority of financial institutions (81%). This is not a surprise, considering the severe consequences these organizations face if confidential data is compromised. According to Ponemon’s 2018 Cost of Data Breach Study, financial services is the industry with the second largest per capita cost of data breach among all industries ($206 per each lost or stolen record). Headlines about financial organizations experiencing data breaches may be the reason why most financial organizations plan to increase their security investments by 157% in the next 5 years and consider better detection of external and internal threats as the key way to improve cybersecurity.
View the full infographics for the 2018 IT Risks Survey and the results for the financial sector here: